PETER HAYES
SEPTEMBER 22, 2021
I. INTRODUCTION
In this essay, Peter Hayes argues that Nuclear Command, Control, and Communications (NC3) in Asia-Pacific is a potent “force multiplier” that makes a given combination of nuclear warheads with delivery systems far more lethal than nuclear weapons considered alone. The importance of NC3 likely increased during the pandemic because of its outsized role in the perception of the credibility of the threat to use nuclear weapons in a crisis and with it, the risk of war in a nuclear-prone conflict. The laws of armed conflict and other international law that define commander accountability on when and if use of nuclear weapons is ever legal demand that procedures that are universally agreed to should be implemented in all NC3 systems.
Peter Hayes is Director of the Nautilus Institute and Honorary Professor at the Centre for International Security Studies at the University of Sydney, and Research Director of the Asia-Pacific Leadership Network.
This paper was presented to Weapons of Mass Destruction (WMD) in the Asia-Pacific Workshop, December 1-4, 2020, Asia Pacific Leadership Network for Nuclear Non-proliferation and Disarmament and published by APLN here The workshop was funded by the Asia Research Fund (Seoul).
The views expressed in this report do not necessarily reflect the official policy or position of the Nautilus Institute. Readers should note that Nautilus seeks a diversity of views and opinions on significant topics in order to identify common ground.
This report is published under a 4.0 International Creative Commons License the terms of which are found here.
Banner image: Global NC3 nuclear threat relationships and linkage. Image is by Lauren Hostetter of Heyhoss Design
II. NAPSNET SPECIAL REPORT BY PETER HAYES
NUCLEAR COMMAND, CONTROL, AND COMMUNICATIONS (NC3) IN ASIA-PACIFIC
SEPTEMBER 22, 2021
BACKGROUND
Nuclear Command, Control, and Communications (hereafter NC3) is one of the least known but arguably most critical dimension of nuclear forces in Asia Pacific. Put simply, NC3 combines wetware (people), hardware (sensor, communications, and control technology), and software (digital code that enables the digital elements to connect people with machines, although much of the technology is analog inherited from a pre-digital era in the older nuclear-armed states). The purpose of this combination is to enable commanders to target, operate, control, and use nuclear weapons by receiving data and advice from sensor systems and people tasked with interpreting it, to make decisions, and to send orders to nuclear forces to move, go on alert, or to strike targets. Most treatments of nuclear forces focus on nuclear warheads (type, number, megatonnage, and fissile material) and delivery platforms (type, range, accuracy, tactical versus theater versus strategic) and simply take NC3 as given. There is a reason, however, that David slung his stone into the forehead of Goliath rather than his musculature. Without a head connected to a body, a nuclear force is useless. Disregarding NC3 misses, it is perhaps the most critical element of making nuclear war. Therefore, it behooves us to pay attention to it.
Also, NC3 is arguably a potent “force multiplier” that makes a given combination of nuclear warheads with delivery systems far more lethal (if the NC3 systems are relatively robust and reliable) or—if destroyed by counter-NC3 attacks—far less able to annihilate an adversary in a first, retaliatory, or indeed, any strike at all (the “perfect” counter-NC3 strike being one that simply decapitates the nuclear forces of an adversary or vastly limits the damage incurred from its forces attacking one’s own forces and/or society). Thus, more capable NC3 may substitute for additional nuclear forces at a given force level, making additional forces unnecessary even when adversarial forces expand or improve qualitatively. Or they may even offset reductions in nuclear forces without reduced threat levels that sustain putative nuclear deterrence perceived by an adversary.
Conversely, “improved” counter-NC3 forces may undermine such perceptions and force-enabling characteristics of NC3, and thereby increase the risk of first-strike instability between nuclear-armed adversaries. The worst case is improved NC3 forces combined with expanding nuclear forces and increasingly effective counter-NC3 forces, implemented either by one side creating an illusion of nuclear escalation and warfighting dominance; or, if implemented by both sides, increasing the perception that going first is the only option to limit damage from the inevitable first strike by a nuclear adversary given their NC3 vulnerabilities.
NC3 does not loom large in arms control or disarmament literature, with significant exceptions. In the American Cold War, use of NC3, which was distilled in the acronym NC3I for nuclear command, control, communications, and intelligence in standard theoretical and policy use in the mid-eighties, NC3 was indistinguishable from NC3I. That’s because NC2—nuclear command-and-control—relied indispensably on communication systems–the third C in NC3—to communicate information from nuclear commanders in the command chain to and from nuclear forces and, in turn, to convey information from sensor systems that provided early warning, target identification, and damage assessment needed for nuclear commanders to make decisions, select strike options, and issue strike orders with nuclear forces.
Because these “national technical means” (NTM) were viewed as integral to sound nuclear decision making and indispensable to the operation of nuclear forces before, during, and after a nuclear war, many US-Soviet strategic nuclear arms control agreements included clauses banning “interference” with NTM. Otherwise, because NC2 and supporting communications systems are so opaque, making it impossible to verify compliance with various measures that might have been taken to control NC3 systems in these agreements, NC3 simply doesn’t appear in strategic arms control agreements. And there are few tacit understandings let alone norms on behaviors related to NC3 and counter-NC3 operations.
Moreover, analysts of NC3 mostly assumed that “more NC3” is automatically better. After all, who could object to increasing negative controls over nuclear weapons (those organizational and technical measures that ensure nuclear weapons are never used by mistake) or positive controls over nuclear weapons (those organizational and technical measures that ensure nuclear weapons are always available for immediate use, the underlying basis of nuclear threat that creates the perception that nuclear retaliation is inevitable and therefore nuclear first use is never rational, the essential foundation of strategic deterrence and “stability” in nuclear threat dyads)? Thus, goes the argument, more NC3 means more bang for the buck at same or lower cost, and less risk of nuclear war due to enhanced strategic stability. So why worry about NC3-related arms control, let alone disarmament?
Unfortunately, this perspective was highly subjective, introspective, and parochial. In reality, nuclear armed states are in a conflict relationship, and a relationship is always based on communication of intention and capability—as was explained long ago by the first generation of strategic theorists. Such communication can take many forms—statements of doctrine, political threat rhetoric, back-channel messages, diplomatic demarche, changes in alert levels, force deployments, forward deployment, nuclear warhead and delivery platform testing…the nuclear practitioner’s repertoire is quite extensive, even for small monadic forces, let alone “mature” triadic forces with global reach deployed by the United States, Russia, and China today. Among the most important information that is sent by one nuclear antagonist to another is that obtained by communications intelligence systems of what an adversary’s nuclear command is saying to its own forces combined with direct observation via NTM of status and operations of deployed nuclear forces. Thus, sensors create information flows that continuously link adversarial forces in what is correctly termed “NC3 interdependence,” thereby creating what a “tightly coupled” US-Soviet NC3 system (Paul Bracken),[1] and a “gigantic interacting system” (Ash Carter)[2] , although they did not analyze the resulting global dynamics of this NC3 “metasystem” even when it was relatively simple during the Cold War.
Today, with 15 nuclear weapons and nuclear-delivery states each endowed with distinctive national and in some cases (NATO) multinational NC3, global NC3 interdependence is vastly more complicated to the point of true complexity and can no longer be ignored. It is now critical that NC3 be analyzed for its direct contribution to the increase or reduction of nuclear risk—depending on the contextual circumstances, and that policy measures be taken to control and disarm NC3 systems, not just the warheads and delivery systems for nuclear weapons. To not do so would be like analyzing the efficacy of global air traffic control systems without revealing the location of air traffic control towers, the frequency, procedures, and language used and harmonized by ICAO, and paying no heed to the communication systems employed to coordinate aircraft movement and to synchronize aircraft movement across whole airspaces under different routine and emergency circumstances. Anyone who proposed running air traffic control without minimal transparency, common standards and procedures, and interoperable communication systems sharing sensor data from radars and satellites would be dismissed or isolated (think airlines that assiduously avoid traversing DPRK airspace). Yet, that is the situation today with respect to NC3.
DEFINITION OF NC3
To proceed, we first need a working definition of NC3. There is no agreed definition of NC3, however between or within nuclear armed states. It’s not even clear that all nuclear-armed states even use such a term. Or if they do, whether it captures the same meaning and scope as its dominant usage in American and allied nuclear forces.[3] The concept is most developed in the United States and its allies, and in Russia, where it has long been the subject of military and budgetary definitions, although these have varied over time.
At a basic and universal level, the NC3 system connects senior nuclear commanders with their nuclear forces and enables them to control their use at all times. Control is a critical concept when it comes to nuclear weapons given their uniquely destructive capability. It is translated by many procedures, measures, and organizational systems, some of which may work against the other when it comes to combining negative and positive controls in routine, crisis, and wartime nuclear weapons operations. Also integral to NC3 is the notion of legitimacy and authority—the nuclear commander must be accountable under domestic and international law. And there must be systems to ensure that command decisions are authenticated and that nuclear weaponeers know that commands that they receive and act on are authentic and legal.
American nuclear weaponeers have long held that NC3 systems must be as reliable, robust, and capable to deter nuclear strikes.[4]
In this view, NC3 is a system. It is made up of all the elements that enable a weapon to be deployed, including appropriately trained personnel, parts, and the systems that allow an NC3 apparatus to work all the way from commander to weapons operator. The fit between the weapon and the NC3 system is never perfect.
The United States made a clear public statement as to what is meant by NC3. The US Department of Defense’s Nuclear Matters Handbook (2020 edition) states:
The U.S. command and control is necessary to ensure the authorized employment and termination of nuclear weapons operations, to secure against accidental, inadvertent, or unauthorized access, and to prevent the loss of control, theft, or unauthorized use of U.S. nuclear weapons. The President’s ability to exercise authorities is ensured by NC3.[5]
It then goes on to state that NC3 can only be understood with reference to NC2:
In order to understand NC3, it is important to define nuclear command and control (NC2). NC2 is the exercise of authority and direction, through established command lines, over nuclear weapon operations by the President as the chief executive and head of state. NC2 is supported by a survivable network of communications and warning systems that ensure dedicated connectivity from the President to all nuclear-capable forces. The fundamental requirements of NC2 are that it must be assured, timely, secure, survivable, and enduring in providing the information and communications for the President to make and communicate critical decisions throughout the crisis spectrum.[6]
Elsewhere, it states more succinctly that “NC3, managed by the Military Departments, nuclear force commanders, and the defense agencies, provides the President with the means to authorize the use of nuclear weapons in a crisis.”[7]
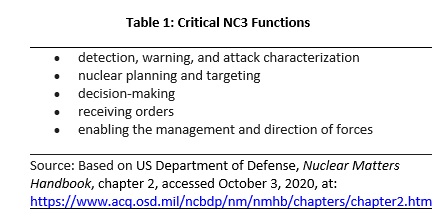
Viewed functionally, DOD states:
NC3 assures the integrity of transmitted information and must be survivable to reliably overcome the effects of a nuclear attack. NC3 performs five critical functions:
- detection, warning, and attack characterization;
- nuclear planning;
- decision-making conferencing;
- receiving presidential orders; and
- enabling the management and direction of forces.[8]
This functional capacity in turn is nested in supporting communication systems:
NC3 relies on terrestrial (e.g., land-based secure and non-secure phone lines and undersea cables), airborne relay (e.g., E-4B and E-6B), and satellite (military and commercial) sensors to transmit and receive voice, video, or data. The ability to move trusted data and advice from sensors to correlation centers, from presidential advisors to the President, from the President to the NMCC, and from the NMCC to the nuclear weapons delivery platforms depends on NC3…These encompass a myriad of terrestrial, airborne, and satellite based systems ranging in sophistication from the simple telephone, to radio frequency systems, to government and non-government satellites. Some of these systems are expected to be able to operate through nuclear effects, while others are expected to be subject to nuclear effect disruption for periods ranging from minutes to hours.[9]
Figure 1 shows this nesting of the various elements of NC3, starting with nuclear commanders at the center, linked to nuclear weapons systems, and linked in turn to external sensor systems by communication systems.
Figure 1: Nested NC3 Systems

Source: Figure 2.2. NC3 Weapon System and AFPEO/NC3 & AFNWC/NC Responsibilities, in “Special Management Nuclear Materiel Management,” Air Force Materiel Command Instruction 90-204, 4 May 2016, p. 10 released under US FOIA request to Nautilus Institute.
These generic definitions of the elements of US NC3 are translated into binding directives by military combatant commands. The US Air Force, for example, states:
NC2.—Nuclear Command and Control, NC2, is the exercise of authority and direction by the President, as Commander in Chief of U.S. Armed Forces, through established command lines, over nuclear weapon operations by military forces; as Chief Executive over all Government activities that support those operations; and as Head of State over required multinational actions that support those operations.
NC3.—Nuclear Command, Control, and Communications, NC3, is the collection of activities, processes, and procedures performed by appropriate commanders and support personnel who, through the chain of command, allow for decisions to be made based on relevant information, and allow those decisions to be communicated to forces for execution. NC3 is a system of systems, stretching across services, combatant commands, and other DoD entities.[10]
This reference to a “system of systems” is important. A system of systems is inherently complex. The US NC3 system is a sprawling patchwork of systems operated by each service, much of which is not inter-operable. And because the US military has three nuclear weapons forces run by its air force (missiles and bombs) and navy (submarine), each with global reach, it really operates three global NC3 systems, plus the fusion of these systems in the decision-support systems that extend to the Joint Chiefs and the US president, and then back to nuclear forces who must act on decisions. This very complexity is subject to the Byzantine Generals problem and may result in unanticipated cybernetic feedbacks, logical flow errors, and inadvertent outcomes.
A simplified, functional definition of the complete meaning of NC3 in terms of supreme commander control of nuclear weapons is provided in Table 1. Arguably, however achieved, these functions are universal among all nuclear-armed states in one way or another.
Before turning to practical, plausible, and desirable NC3 policy measures, we need to first survey the uneven terrain of NC3 in the Asia Pacific region that captures seven of the nine nuclear-armed states (Russia, China, the United States, Israel, Pakistan, India, North Korea) that are inextricably linked by mutual nuclear threat relationships.
Before analyzing what must be done with respect to NC3 to reduce the risk of nuclear war and to resume nuclear disarmament in the current context, we first describe the NC3 systems of each nuclear-armed state in this region.
NC3 SYSTEMS IN ASIA PACIFIC
US NC3
NC2 (defined above as nuclear command and control) is conducted in nuclear command posts, the most important of which are in the White House, the National Military Command Center at the Pentagon, at Strategic Command HQ in Omaha, and at the unified command HQs in Hawaii and NATO HQ in Brussels. These are supplemented by a variety of mobile command posts, including presidential and the Air Force E-4 National Airborne Operations Center, the Navy’s E-6 Mercury TACOMO aircraft, and various lang-based mobile backup centers (see Figure 2).
Figure 2: National Military Command System Connectivity to the Forces (2001)
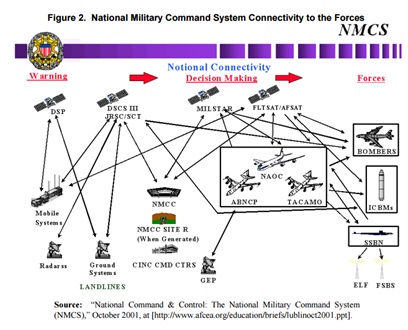
Source: Robert Critchlow, Nuclear Command and Control: Current Programs and Issues, Congressional Research Service, RL33408, May 3, 2006, p. 7.
NC2 is supported and connected across nodes and with sensor and early warning systems on the one hand, and nuclear forces on the other, by a range of communications systems, adding the third C to NC3. These systems provide connectivity to NC2 whereby data and messages are sent via wireless and cable, some dedicated to nuclear forces, some shared with non-nuclear forces. The wireless networks use the entire spectrum from extremely low to ultra-high frequencies. Some are line-of-sight, some wrap around the Earth, and some are directed at satellites and are then sent back down to ground receivers or sideways to other satellites before being sent back to Earth. Some frequencies are hard to interfere with, while some work better in an atmosphere “perturbed” by nuclear detonations. Some have been hardened against the electromagnetic pulse emitted by a nuclear detonation while many have not, and some are able to penetrate the surface layer of the ocean to reach submarines. Antenna size and weight determines which delivery platform can use with which frequency-based system. In the digital era, NC3 now includes computer and cyber systems that are integral to computation, fusion, and transmission of data and messages over connectivity provided by digitized communications systems.
Over seven decades of nuclear warfare, each military service has developed its own communications systems, many of which are not able to be received by those of the other service. That is, they are not interoperable. The same problem arises with regard to nuclear allies within NATO and other US nuclear umbrella states such as Japan and the ROK. Figure 3 shows the NC3 systems operated primarily by the US Air Force. Figure 4 shows the NC3 systems operated primarily by the US Navy.
Figure 3: US Air Force and Other NC3 systems
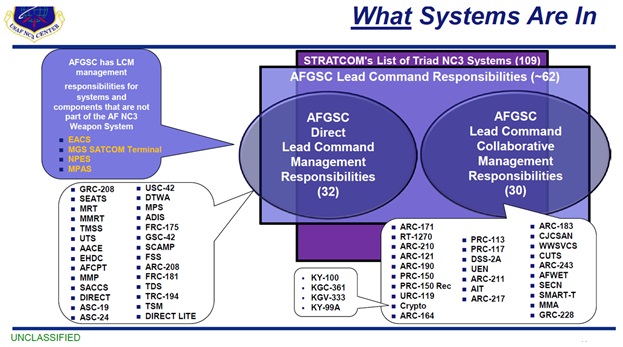
Figure 4: US Navy Strategic Communication Systems 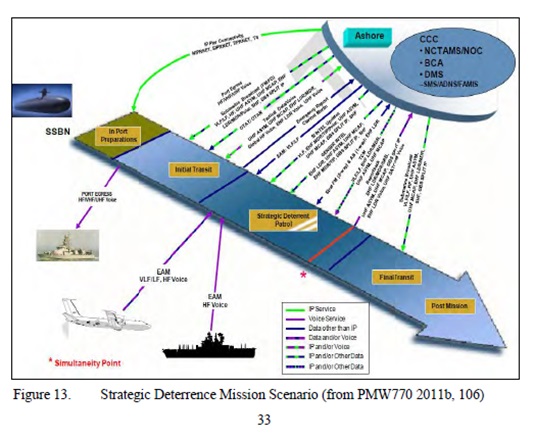
Source: “Figure 13 depicts the nuclear command, control and communications (NC3) infrastructure needed for mission communications while performing a strategic deterrent patrol. The BCA [broadcast control authority] provides the interface to the NC3 system for delivery of EAMs. Take charge and move out (TACAMO) aircraft and surface ships relay EAMs [emergency action messages] if there is a failure of the primary reception paths. The simultaneity point indicates when multiple communications paths will be available for use.” M. Seime, Common Submarine Radio Room: A Case Study of a System Of Systems Approach, thesis, Naval Postgraduate School, 2014, p.33, at: https://calhoun.nps.edu/handle/10945/43998
This global nuclear decision-making and communications apparatus would be useless without the ability to sense via many means the state of the world. The most important US nuclear sensors are those that provide early warning of nuclear attack. The earliest warning of missile attack comes from satellite-based infra-red sensors that see the heat of missile launch and exhaust. From forward-deployed radars, it would get the earliest confirmation by a physically disparate sensor if in range. If not, arcs of long-range radars in Alaska, Greenland, the UK, and on the three coasts of continental United States, supplemented by ballistic missile defense and NATO radars plus radars monitoring space, serve to identify missile launches and against whom they are targeted.[11] A nuclear detonation detection system also operates in the United States to confirm actual nuclear attack on the United States. All this warning from 24/7 monitoring converges on ground stations where it is assessed continuously for false alarms or discounted as non-missile events, notably in the National Military Command Center in Washington, DC, the Global Operations Center at Offutt AFB, NE, and the headquarters of the North American Aerospace Defense Command and Cheyenne Mountain in Colorado.
When the nuclear communications infrastructure is combined with the nuclear command system, it is truly vast—so much so that it exceeds the ability of managers to grasp. As the Defense Information Systems Agency—the entity within the US Department of Defense responsible for integrating all these elements to ensure that nuclear command-and-control provided the necessary connectivity between national command authorities and nuclear forces—stated in 2010, “There is no one NC3 system. The NC3 system as it exists today is a patchwork of disparate systems, each with its own characteristics. There is no one operating system or coding language.[12] The true complexity is revealed in the evolution of estimates of the number of systems that constitute NC3. In 2017, for example, US General Robin Hand stated that “There are a huge number—107 different systems to get our hands around.”[13] In 2019, a STRATCOM official estimated that there were 109 such systems.[14] At the same workshop, Jeffrey Larsen stated, “ Depending on who you ask and how they count, the US NC3 system consists of as many as 160 different systems: satellites, aircraft, command posts, communication networks, land stations, radio receivers, and so on—a system of systems perhaps too complex for any one person to totally understand. “[15] By 2020, US Under Secretary of Defense Ellen Lord testified,“The NC3 portfolio comprises a complex architecture of more than 200 systems that allow detection of threats, support decision making, and enable force direction.”[16] As a senior commander in charge of US NC3 systems stated in 2019, “I am confident that the NC3 system will work. I just don’t know how and why it works.[17]
Russian NC3
NC2 in the former Soviet Union, now Russia, is dominated by the need to command and control the long-range nuclear missiles that constitute the bulk of its nuclear forces. A substantial fraction of these missiles is located in Siberia, far from the high command in Moscow. Russia also operates missile firing submarines but generally keeps them close to home-based anti-submarine forces to provide some cover against US forces tracking Russian submarines from air and sea. It also has long-range bombers that—like their American and Chinese counterparts—need communication systems at long-range. In the past, Russia based intermediate range rockets in the Far East, but these were removed under the Intermediate Nuclear Forces treaty, leaving only shorter range missiles along the border with China, some bombers, and a strategic missile submarine force that has been reconstituted in Kamchatka after a long period at the end of the Cold War, when no such forces operated in the Russian Far East/Pacific region.
Russia’s primary modern nuclear command post, the National Defense Command and Control Center, was opened in 2014 and contains within it the Nuclear Strategic Forces Command and Control Center. This Center manages nuclear weapons operations as directed by Russia’s political and military leaders.[18] Russia has two, possibly three underground nuclear command and control bunkers, one at Kosvinsky Kamen in the Northern Ural Mountains, and another at Mt. Yamantau in the Southern Ural mountains (the latter may have shut down and likely was a government continuity relocation site similar to the US Rock Raven facility outside of Washington, DC). Each of the military services (Strategic Rocket Force, Navy, Airspace Force, and the Army has its own command post with communications and computing support. In November 2020, Russian President Putin revealed that Russia has activated a new underground nuclear command bunker and, like the United States, also has stationary and mobile command posts spread across the country.[19] How many of the dispersed nuclear command posts around Moscow (said to be about eighty in the early 1980s) remain today is unknown.[20] How many of the dispersed nuclear command posts around Moscow (said to be about eighty in the early 1980s) remain today is unknown.[21]
Figure 5: Former Soviet Union Strategic Communications Systems (Airborne Left, SSBN Right)
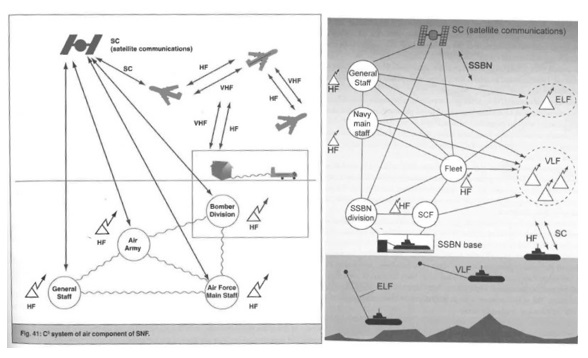
Source: V. Yarynich, C3I: Nuclear Command, Control Cooperation, Center for Defense Information, Washington DC, 2003, p. 135 et passim, at: https://www.scribd.com/doc/282622838/C3-Nuclear-Command-Control-Cooperation
Russia’s strategic communications relied on an extensive array of radio and cable communications across frequencies and media to link these command posts with nuclear forces located across eleven time zones. Communications included landlines, radiotelephone, microwaves, and satellites. The mainstay of connectivity was long-haul HF communications which was then supplemented by satellites operating in low orbit and in elliptical orbits during the Cold War.
The system also reportedly has an automated launch system as well as a rocket. These were to be fired as a last resort and were dedicated to transmitting fire orders in extremis to nuclear forces should Russia’s nuclear command posts be incapacitated or destroyed in a war.
As American nuclear forces shifted from bomber to missiles in the early 1960s, the former Soviet Union developed its early form of missile-detection radar. These became operational in 1970 in the form of two “Dnepr” radars near Murmansk and Riga and the Command Post near Moscow. The former Soviet Union {FSU] also began to develop its early warning satellites, although these remained far behind American satellite capabilities to provide a two-echelon missile tracking system that provided 360-degree monitoring along all borders. At the end of the Cold War and throughout the 1990s, the now-Russian early warning system more or less collapsed. For a period, Russia operated its forces without any operating early warning satellites, and the radars were also degraded by age, lack of funding, and de-staffing. In 2014, the decaying legacy satellite system was down completely,[22] leaving Russia solely reliant on its old radars.
Today, Russia has deployed two new modern Voronezh radars and a new constellation of early warning satellites known as the United Space System, or EKS, that have restored Russia’s ability to detect early and confirm missile attack. However, by admission of the experts contracted to construct the system, it remains error-prone, especially the ground components.[23]
Overall, the Russian system is far flung but highly centralized and top down compared with the relatively flat and distributed American nuclear command and control system. During the Cold War, the former Soviet Union’s (hereafter FSU) pyramidal structure made the Russian system prone to an error made at the top and center that is propagated quickly throughout the whole system, whereas the American system, being more devolved into regional commands, tends to not propagate errors across different parts of the world. Whether this remains the case today is an interesting question.
Chinese NC3[24]
Like Russia, China’s NC3 imperatives are dominated by its small land-based nuclear missile force. Unlike the United States and Russia that sport a triad, China has been a monad until recently when it began to develop a naval (strategic missile submarines) leg,[25] and a possible dual-capable long-range aerial (bomber) leg. China’s NC2 system is Chinese Communist Party-controlled. They make nuclear weapons decisions in conjunction with the People’s Liberation Army (PLA), which operates the Second Artillery Force since 1966 that fielded nuclear missiles, renamed the PLA Rocket Force in 2016. Their leading policy that shaped its NC3 system was to field a small nuclear force sufficiently robust to retaliate after absorbing a first strike from a nuclear adversary, such as the United States, and after 1969, the FSU.
In 1986, the PLA established the Central Emergency Command Center (CECC) for continuity of government under attack. The primary underground hardened site built inside a mountain under Yuquanshan in Xishan outside Beijing, with two sub-centers reportedly at Wuwei (Langzhou military region) and Mianyang (Chengdu military region, later increased to five nodes with the addition of Taiyuan (Beijing military region), Luushan (Jinan military region), and Weining (Chengdu military region). Other military command bunkers reportedly existed in Inner Mongolia Autonomous Region along with another 29 hardened bunkers connected by cables.[26]
In the early decades of nuclear armament, China used primarily radio communications and telephony to connect nuclear commanders with forces. Starting the 1990s, the PLA laid much fibre-optic cable and integrated microwave communications. Starting the early 1990s, China used DFH commercial satellites for military communications, and deployed its first military FH-1 military communications satellite in 2000, now supplemented by fiber-optic cables laid in the 1990s, and satellites.[27]
China’s communication systems are dual use, supporting conventional and nuclear traffic between nuclear commanders and forces. Since 1998, China has semi-automated the issuance of nuclear strike orders and related messages to mobile missile brigades housed in underground tunnels or on the move, allowing central commanders to monitor movements and launches. Once China sends its strategic missile and nuclear attack submarines into the open ocean, it will use low frequency radio towers and transmissions to communicate orders, supplemented by airborne relay systems and satellite downlinks. Mobile missile launch units moving freely on the surface may be assumed to have field communication networks including telephone, videoconferencing, and command networks over wireless and satellite networks.
Because China’s nuclear forces are configured to launch only after nuclear attack, it has historically had only minimal early warning radar coverage. As Cunningham explains:
China has three phased array ground-based radars, similar to U.S. PAVE PAWS radars, located in Heilongjiang province in the country’s northeast, Fujian province in its southeast, and Xinjiang in its northwest. Improving China’s strategic warning capabilities was an explicit priority for the PLA in China’s most recent 2015 defense white paper. China has no space-based missile attack early warning system but is likely to be developing one. A space-based early warning system would enable China to shift to a launch-under-attack alert status if it chose to do so in the future. A Chinese space-based early warning system is, however, unlikely to be operational for approximately another decade.[28]
The same retaliatory doctrine of launch-after-or-under-nuclear attack only requires China to be able to detect a nuclear attack. This reportedly was built starting in 1974 and is a national reporting network of enormous significance to the credibility of China’s nuclear force. [29]
DPRK NC3
In comparison with the great powers that are nuclear-armed, DPRK’s nuclear command and control system is relatively simple, as is its current force structure and supporting connectivity.
DPRK law states clearly that Kim Jong Un is the supreme nuclear commander of the DPRK. In 2014, the Strategic Rocket Command was renamed and became the Strategic Forces Command. This change was to create a direct chain of command from Kim Jong Un to nuclear forces via automated missile launch systems to ensure that his orders are followed.[30] Having only land-based intermediate and largely untested long-range missiles capable of delivering nuclear weapons, the DPRK has a nuclear monad, although it has begun to develop submarine-launched missiles that could carry nuclear weapons in the future.
The DPRK has likely built an NC3 system that is dedicated solely to nuclear forces, both to preserve Kim Jong Un’s sole control and to avoid any risk of loss of control due to organizational cybernetics or confusion arising from dual use communications and weapons systems that pose issues of queuing and priorities for message delivery. Although the high echelons of the DPRK military at the Joint Chiefs and Corps-level commands reportedly use computer-based C3 systems, this does not extend to lower echelons in the conventional military, which relies mostly on telephone, radio, cable, and couriers, with fiber optic extending to forward echelons. However, fiber optic cable is likely to have been laid between the supreme command and missile and warhead bases, and from these bases to preselected sites for transporter erector launchers, to wait and receive orders that may be dispatched with very short time frames from decision to launch, given the complete lack of long-range early warning systems in the DPRK that would identify and respond to a US nuclear attack.
Similar to China, the DPRK’s NC3 system includes a party control element at each critical point to ensure political loyalty and compliance with directives from above. It is likely that the DPRK’s warheads are not mated to its missiles most of the time and are kept under the control the Korea Worker’s Party’s Central Military Committee. When ordered, a nuclear ordnance unit would receive warheads under party control and transfer them to missile units for mounting them. This transfer is a particularly fraught and perilous aspect of control in the DPRK NC2 system, and political commissars surely play a key role in ensuring that this integration is achieved during exercises and would do so in wartime.
Indian NC3
Not much tangible may be said in this section for the simple reason that there is almost no country-specific data about the NC3 architecture in India.
NC3 in India is understood to support the Nuclear Command Authority that manages its nuclear and missile forces and would authorize use of nuclear weapons with an operational command base established as early as 1998 on the outskirts of New Delhi.[31] But the command post locations, nodal-network structure, and its multiple, service-based[32] and likely non-interoperable communication systems have not been described in any detail in open source.
Given that India has an advanced scientific and engineering infrastructure and a globally competitive IT sector, one can safely infer that its current NC3 system relies heavily on cable, especially fibre-optic cable, microwave links, and radio links, including non-dedicated satellite links between nuclear warhead sites, sufficient to support dispersed missile launcher sites and fighter-bomber units on various airfields.[33] However, how effective such communications for mobile nuclear weapons has become remains an open question.[34] According to former advisor to India’s Prime Minister, Shyam Saran, India’s nuclear command authority is connected to forces with radiation hardened, redundant, and secure nuclear communications systems with “back-up” facilities.[35] Indian Cabinet Committee on Security reportedly has approved the construction of alternate chains of command, implying multiple command sites and communications systems for the contingency of loss of the primary nuclear command and control system.[36] India’s Strategic Forces Command, according to one blogger, “provisions the primary and alternative command posts, operations rooms, and communication.[37]
India also now operates missile-launching submarines and, in 2014, activated a naval very low frequency (VLF) transmission station for communicating with the deployed submarine at Kattabomman in Tamil Nadu on the southern tip of India.[38] In 2017, the Indian navy announced it would build a second VLF transmitting facility at Pudur in central India.[39]
India has two potential nuclear adversaries to monitor, Pakistan and China. In 2002, India acquired missile warning radars from Israel and reportedly deployed two of these units, which have been upgraded to support ballistic missile defenses.[40] Given range limitations and the extremely short flight times of missiles fired from Pakistan, these radars have limited utility of providing meaningful early warning to India of attack from either Pakistan or India. India’s satellite capabilities provide enhanced strategic warning but are limited in their technical capacity. Electronic, communications, and human intelligence will factor into India’s decision-making calculus more than long-range sensor systems, although its expanding space program may shift this balance in its NC3 system.
Pakistani NC3
As with India, little is known publicly about Pakistan’s NC3 system. Like India, the NC2 or nuclear high command organizational structure is reasonably understood. As Feroz Khan summarizes this system:
At JSHQ [ Joint Service Headquarters], the communication systems of the three services, along with civilian and military intelligence agencies inputs, are integrated to produce a net assessment of threats that is available to the highest civilian and military leadership. JSHQ is responsible for the organization and functioning of the National Command Center (NCC), which links the conventional force military operations, naval operations, and air force operations into an integrated system (CC3). After SPD was formed, its C2I2 SR Directorate evolved a dedicated nuclear (strategic) communication system (NC3). At NCC, a common operational picture (COP) is available that merges all national surveillance and reconnaissance capabilities, integrating satellite, drones, and other information means from all three services. The communication system is backed with several redundancies and is a secure, dedicated communication system with procedures that are updated as the information age evolves and new innovations in cyber, space, and information technology domains are introduced.[41]
However, the actual physical infrastructure of command centers, communication nodes and networks, and early warning systems has not been described in open sources in recent history. Shaun Gregory provides the best—albeit very dated—description of the communication system that supports Pakistani NC2:
Pakistan relies on a variety of space and land-based communication systems to assure nuclear connectivity and the continuity of centralized control. Some of these systems are commercial and others dedicated military networks. System robustness is underpinned by redundancy, the simple idea that if one or more systems fail others will be available to take their place. Pakistan’s PASCOM network provide peacetimes army-wide land-line and, for GHQ and corps HQ, mobile phone connectivity; the DEFCOM and PATCOM networks provide satellite, fibre-optic, microwave and switching system connectivity; while the SATCOM network enables corps connectivity through VHF vehicle radio sets, field exchanges and faxes. Pakistan has also been the recent beneficiary of US tactical communications system upgrades – most notably Falcon II, to enable better US–Pakistan interoperability in the war on terror. Despite these arrangements, connectivity through the stages of conflict escalation to the nuclear level is not assured. At least four factors undermine system robustness in Pakistan: (1) the high costs of ensuring full-network redundancy; (2) the technical fragility of communication systems; (3) the vulnerability of the nuclear communication networks and nodes to electronic counter-measures, physical assault, technical dependency; and (4) the particularly rigorous demands of mobile basing.[42]
Pakistan’s satellite capacities are also feeble[43] and the entire network appears highly vulnerable to disruption, counter-measures, and physical attack. At least part of its commercial fiber-optic network traverses India although it has dedicated military fiber-optic cables to support conventional forces. Even with codes, radio is considered unsafe for strategic communications, so it is likely used only for routine communication for NC2 purposes, if at all.
Like India, Pakistan has deployed a missile firing submarine and built a VLF station at Hameed near Karachi to communicate with it at sea.[44] The vulnerability of this facility and the demanding communications requirements of mobile missiles and possible deployment of tactical, forward-deployed nuclear weapons near the border with India raises the troubling possibility of early delegation of use authority to forward commanders in a crisis.[45]
Likewise, Pakistan’s early warning system has limited range and is fragile. It has access to commercial satellite photography but for military purposes, depends almost entirely on US and China for strategic satellite support in a crisis. Its air defense radars are short range and provide limited warning of incoming aircraft or cruise missiles aimed at disabling its NC3 nodes and networks.[46]
KEY NC3 ISSUES
The preceding sections defined NC3 as a critical dimension of nuclear forces, and outlined the NC3 systems, including early warning systems, of the five nuclear-armed states in the Asia Pacific region. This section introduces six key NC3 issues: (a) the contribution of NC3 to the risk of nuclear war; (b) NC3 modernization and disruptive technology; (c) nuclear decision-making and commander accountability under international law pertaining to NC3; (d) complexity and the global NC3 system; and (e) the pandemic-nuclear nexus and NC3.
NC3 and Nuclear Risk
In section 2, we noted that NC3 is a force multiplier that represents a threat to a targeted state due to its ability to enhance the lethality of nuclear forces and to fight nuclear wars that are less than all-out global paroxysms of nuclear violence that end human existence. NC3 missions in this limited nuclear war context include precision targeting of adversarial NC3 sites and systems to stun and degrade its ability to retaliate with nuclear attacks, retargeting weapons on new targets based on intra-war intelligence (reallocating weapons from already empty silos and already annihilated targets onto new targets such as missiles on the move), terminating nuclear war operations, and reconstituting own forces to prepare for the next war. These NC3 attributes lead to two types of operational problems.
The first is the vulnerability of many parts of the NC3 system. Although nodes can be buried in mountains and network hardware can be hardened against nuclear effects such as electro-magnetic pulse frying of electrical circuits and electronics, nuclear detonations are so powerful that once nuclear war begins, no-one knows if and for how long nuclear command and control will continue, or if it will continue at all.
Nuclear-armed states responded to vulnerability with a combination of hardening and proliferation of transmitting and repeater sites and redundant networks to make it impossible for a rational adversary to entertain the idea that a disabling strike on NC3 was a practical option. All that a nuclear-armed state has to do is to create a sufficiently resilient system that it can get out some nuclear strike orders to forces to “rip off an arm,” that is, cause sufficient damage to an adversary to deter it from ever attacking—even if it has already destroyed its enemy with a first strike. Nonetheless, the reality is that for all the billions of national treasures invested in NC3 hardening, the sheer explosive, thermal, and radiative power of nuclear detonations is likely to rapidly degrade even the best NC3 system.
For this reason, many NC3 practitioners argue that the primary concern for nuclear risk is not the vulnerability of NC3 systems, but their propensity to cause errors of two types.[47] The first is a false negative error, that is, the nuclear commanders are told by early warning systems that they are not under attack, when in fact they are, and they fail to launch in retaliation. The corrective for this type of error is to invest heavily in strategic and tactical surveillance and reconnaissance sensors and reporting systems, which nuclear-armed states have done in different and highly uneven ways. The failure to notice that the former Soviet Union had emplaced nuclear armed missiles in Cuba was a slow-motion version of this error as the Cuban Missile Crisis might have been avoided if this activity had been flagged before the missiles arrived or were installed.
The second is a false positive error wherein nuclear commanders are told or come to believe that they are under attack when in fact they are not, but they go ahead and launch anyway against another state. There are many examples of this kind of error in the historical performance of US and Russian NC3 systems. Often these false positives are based on hardware or software failure, or human error.[48] In other cases, they are inadvertent due to organizational cybernetics and procedural flaws whereby even a perfectly performed sequence of actions still leads to failure due to the sequencing of the steps between different parts of the organization, or its interaction with the adversary in an unanticipated way.[49] An especially pernicious variant on the false positives that may afflict NC3 systems is the problem of third-party catalysts who set out to induce a nuclear war between two or more other nuclear-armed states in the hope that they will come out unscathed or on top after a nuclear war. (There is a non-state version of this problem, which is the apocalyptic terrorist entity that seeks to end the world for a religious or other reason[50]).
The final way that nuclear risk is affected by NC3 is by malevolent or disloyal elements that may disrupt nuclear operations. The former is exemplified by non-state actors such as terrorists seeking to wrest control of nuclear weapons or delivery platforms as has occurred multiple times in Pakistan already. The latter refers to the possibility of coups in which nuclear weapons are not centrally controlled as may have happened with the attempted coup during the Algerian war in which nuclear warheads were vulnerable to seizure at the French testing site in the Sahara[51] and during the attempted coup against former Soviet President Mikhail Gorbachev when it was not clear who controlled the nuclear codes.[52] These are examples of the Byzantine General problem wherein network dynamics and individual components generate random control failures that cannot be anticipated in advance nor controlled in the moment. In the NC3 system, this problem is one in which one of the command elements controlling nuclear weapons is traitorous to the supreme command, but no-one knows which, making coordination dangerous. The most extreme version of this problem is when a supreme commander turns out to be an agent of a hostile state or becomes insane but retains formal command over nuclear forces. President Trump may have been the first example of this version of the Byzantine General problem turned on its head.
NC3 modernization and disruptive technology
All the nuclear-armed states in the region are modernizing their nuclear forces, whether they are recent arrivals or originate in the mid-twentieth century. The nuclear great powers, especially the United States, China, and Russia, combine old analog with digital computer and communications systems and an array of platforms for transponders and sensors on Earth and in Space. Onto this combination of modern digital-legacy analog, they are superimposing and grafting on rapidly emerging technologies including drones, cyberwarfare, and highly automated data processing now moving into artificial intelligence and early applications of quantum computing and communications.[53] These new technologies have the potential to disrupt existing NC3 systems.
By enhancing NC3 operations, these new technologies may reduce negative and positive errors, thereby reducing nuclear risk; but they can also potentially reduce confidence in the resilience and robustness of NC3, stimulating notions of early first use of nuclear weapons to limit damage in the face of apparent nuclear attack by an adversarial nuclear-armed state. To the extent that these new technologies are driven to enhance conventional military forces, they also create an increased risk of nuclear-conventional entanglement whereby an adversary sees conventional operations as nuclear and feels obliged to act first to avoid being pre-empted.
A new dimension of NC3 is the way that commanders, especially the supreme commander, is not only supported by the classified, vertically compartmentalized and official NC3 systems but is also embedded in social media, which may be used for official signaling of nuclear threat and is linked to early warning systems that monitor social media for indicators of nuclear threat such as mobile unit movements, etc., with obvious potential to enhance false positive errors in the interpretation of nuclear attacks.[54]
Nuclear Decision-Making and Commander Accountability
All organizations, including militaries armed with nuclear weapons, are made up of individuals interacting in patterned behaviors that becomes routines, standard operating procedures, and often guided by historical lessons such as how the last war was fought. They all have commanders at the top that make the ultimate decision on whether to use nuclear weapons—or not. Apart from different cultural orientations and historical trajectories, however, the individuals that rise to the top implement very different versions of what may be called the “n-person” rule, that is, how many people must participate in the decision, how that final decision is made, and who, if anyone, has veto power.
Table 2: Nuclear Command Authority Decision Models
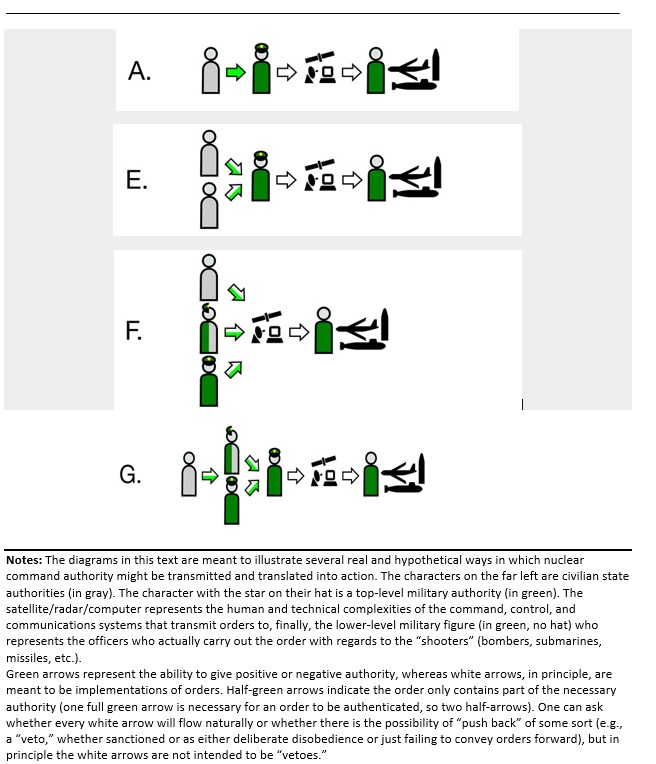
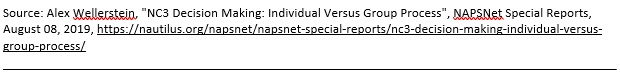
Table 2 above shows representations of simplified decision-making agents produced by Alex Wellerstein. Each diagram portrays who makes the ultimate decision to fire nuclear weapons (see notes to Table for detailed explanation) Diagram A shows how the system works in the United States and likely also in the DPRK. In this absolute nuclear rule model, only the president and the DPRK’s Supreme Leader (currently Kim Jong Un) can order a nuclear strike, which then goes to the top military officials who send the order out to nuclear forces. There is no military or civilian authority or figure who must first sign off or who can countermand this order. A manifestly illegal order may be disobeyed under international law, but that may not stop a determined supreme commander from circumventing an official who says no.
According to Wallerstein, this same one-person rule may also operate in India and Pakistan:
In India, this authority resides in the Prime Minister as head of the Political Council of the Nuclear Command Authority. In Pakistan, the nuclear capability was initially vested in the President of Pakistan as head of the National Command Authority, but it transferred (first procedurally, then legislatively) to the Prime Minister in 2010. It is unclear if these systems look like the flow in diagram “A,” but they may.[55]
In China (see Diagram E) the heads of two civilian committees are required to initiate nuclear use. As the same person (President Xi) is currently the head of both committees, this system of checks reduces to a variant of A, absolute nuclear authority.
In Russia, paraphrasing Alex Wellerstein, three people (the president, the minister of defense, and the chief of general staff) carry the codes that enable them to authorize a nuclear strike. And, at least two “votes” are necessary, portrayed by one full green arrow). States Wellerstein:
Whether any one of these votes is privileged (e.g., is the President always required?), is unknown. Note that the Minister of Defense frequently has military rank, but this is not required (and several have not been military personnel), hence their ambiguous representation here. The Chief of General Staff has always been a high-ranking military officer. The activation of the “chegets” [nuclear codes] appears to go directly into the communication systems without an intervening officer.
It’s possible that the Russian president may have special voting powers in this schema such that only that figure can initiate the order, but at least one of the others must concur, in which case some form of veto exists over the absolute power to fire nuclear weapons. (see Diagram D).
President Trump’s turbulent and uneven use of nuclear threat has raised the issue of whether absolute power to start nuclear war should lie with only one person. As is evident from this overview, however, the n-person question is universal, and some international consensus to generate a new norm on this score is badly needed. Moreover, the laws of armed conflict and other international law that define commander accountability on when and if use of nuclear weapons is ever legal demand that procedures that are universally agreed to should be implemented in all NC3 systems. This will ensure a minimum of accountability in the form of checks and balances to block manifestly illegal and insane strike orders from being implemented, ever. It is for this reason that the Treaty for the Prohibition of Nuclear Weapons includes NC3 systems in its scope, although it has yet to develop a practical set of recommendations that would allow NC3 systems to align with the core values of this treaty, even during the disarmament period when NC3 becomes more important than ever due to the vulnerability associated with holding small nuclear forces that reduces the assured ability of a nuclear-armed state to retaliate against a pre-emptive strike.
Complexity and the Global NC3 System
None of these NC3 systems, including their early warning and decision-making structures, exist in splendid isolation. Each is part of at least one nuclear-prone relationship constituted in part by the projection of mutual nuclear threat.
During the Cold War, this global threat and NC3 system was relatively simple, being either two or three way, depending on when China entered the picture (and subsuming the UK and France into the anti-Soviet bloc). At the time, Paul Bracken argued that the two NC3 systems were inextricably linked and tightly coupled, and the activities of one could generate spastic or pathological responses in the other, in a series of spiraling, interdependent effects whereby NC3 could be both cause and effect of the risk of nuclear war (see Figure 6).
Figure 6: Bracken’s Strategic Force Coupling (1981)
 Source: P. Bracken, The Command of Strategic Forces, Dissertation, Yale University, 1982, p. 39
Source: P. Bracken, The Command of Strategic Forces, Dissertation, Yale University, 1982, p. 39
Also writing in 1982, Charles Perrow argued that when complex systems such as NC3 are tightly coupled and interact, then meta-system will lead to unpredictable effects that emerge rapidly. This was a succinct description of the US-Soviet nuclear weapons systems operating with launch-under-warning postures during the Cold War, which led to a number of hair-raising experiences involving nuclear weapons.
The essential dilemma, writ large today in an era of conventional-nuclear “entanglement,” [56] is that when complex systems are loosely coupled to prosecute conventional war, outcomes are often splintered and delayed as shown in Figure 7 below—to which the appropriate command-and-control response is to devolve authority and responsibility. In the complex world of nuclear war and NC3, in contrast, the rapidity of cascading outcomes demands tighter and more centralized command-and-control with even more meticulous specification of detailed procedures and direction, which leads to even tighter coupling—a looping that eventually causes catastrophic failure. As Perrow puts it, “tight coupling requires centralization, but interactive complexity requires decentralization; and it is difficult, perhaps impossible, to have both simultaneously.”[57] This is exactly what we have in the NC3 systems of the great powers that mix and match “dual use” NC3 and weapons systems that may be armed with conventional or nuclear weapons.
Figure 7: Perrow’s Coupling-Complexity Interaction Models
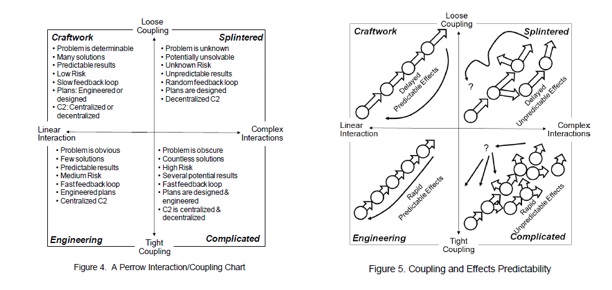
Source: H. Shoults, Organizational Systems Theory and Command and Control Concepts, US Army War College, Carlisle Barracks, March 2013, DTIC accession ADA589438, pp. 10-11, at: www.dtic.mil/dtic/tr/fulltext/u2/a589438.pdf and derived from C. Perrow, Complex Organizations: A Critical Essay, Random House, New York, 1986, pp. 146-154
In the post-Cold War period, the interactive global NC3 metasystem if far more complex than it was in the 1980s. Figure 8 shows the set of six nuclear threat relationships in this region. In this global-regional network of nuclear threats, United States has three, with Russia, China, and the DPRK, as does China (with India, the United States, and Russia). Russia (with China and the United States) and India (with Pakistan and China) have two. Pakistan and North Korea each have one (with India and the United States respectively).[58]
Thus, a nuclear crisis or actual war in Northeast Asia involves the virtual effects of nuclear threats from four nuclear-armed states (United States, Russia, China, and the DPRK). In South Asia, India-Pakistan is linked with China to the East via the China-India threat relationship, and with Israel to the West with their nuclear-laden antagonism. In turn, these regional “threat complexes” are bridged via China which may be involved in simultaneous nuclear crises in both directions while also looking over its shoulder at Russian nuclear forces that retain an element of nuclear threat to China along the Sino-Soviet border in Siberia and the Russian Far East.
Figure 8: Nuclear Threat relationships 2020

Source: Sophia Mauro for Nautilus Institute. This graphic shows the pandemic distribution from COVID-19 Dashboard by the Center for Systems Science and Engineering (CSSE) at Johns Hopkins University (JHU) on September 25, 2020, and the nuclear threat relationships between nuclear armed states.
There is a priori reason to believe that NC3 systems may converge over time due to diffusion of technology on the one hand, and mimesis, or the attempt by latecomers to emulate and replicate the “latest greatest” NC3 setup of the “mature” nuclear-armed states. Conversely, the NC3 systems described in section 2 vary greatly in scale, diversity, capacity, reliability, and reach.
One way to capture the effects of these diverse attributes is to posit NC3 orientations towards positive versus negative controls over nuclear weapons using technical and organizational-procedural measures, an approach pioneered by Jerry Conley.
Negative controls ensure that nuclear weapons are never used except by authenticated intention of legitimate nuclear command authority. Positive controls ensure that nuclear weapons are always available for use by these authorities. This orientation (also termed “control bias”) varies according to the nuclear-armed state’s size, resources, regime type, and external threat environment. Thus, a great power with more than one nuclear adversary may have NC3 systems benchmarked for fighting more than one nuclear war at a time; or to be able to meet the threat of the most potent nuclear adversary leaving it with NC3 capacity to spare most of the time to attend to lesser states. Figure 9 below shows how poor, wealthy, small, large, military-run states may emphasis negative versus positive and procedural versus technical controls. The United States represents the most mature, complex, and capable NC3 system and sits at the middle in non-crisis, routine time.
Figure 9: NC3 State Types by Nuclear Weapons Control Biases
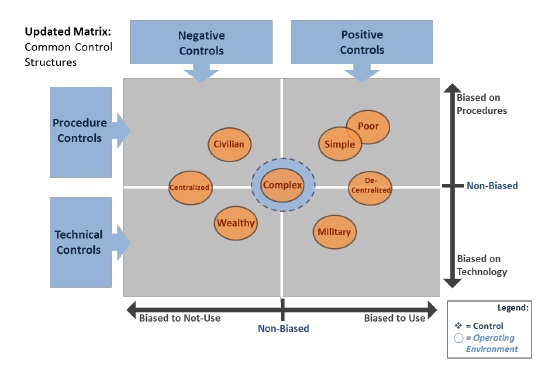
Note: according to dominant characteristic shown in orange circle; also, real states may exhibit more than one characteristic.
Source: Virginia Tech Applied Research Corporation, Nuclear Command, Control, and Stability Framework, December 29, 2016, p. 30, at: https://calhoun.nps.edu/handle/10945/48707
In Figure 10, we see how a trigger event, in this case a terrorist nuclear attack by a non-state actor in Northeast Asia, may shift four nuclear armed states towards an emphasis on positive controls and procedural controls while reducing technical controls and negative controls—that is, they are preparing to release and fire nuclear weapons.
Figure 10: Postulated Impact of a Terrorist Nuclear Threat or Attack on Interstate Nuclear Weapons Controls
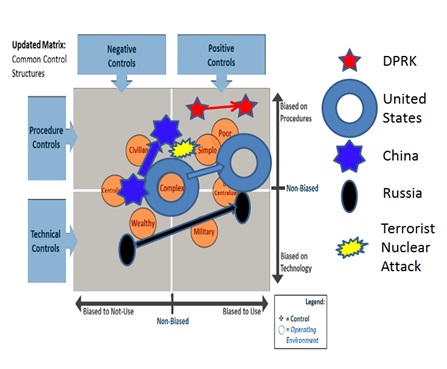
Exactly how this transition from routine to wartime NC3 operations unfolds and how the NC3 systems interact as nuclear forces are placed on alert and/or redeployed is specific to historical circumstances and requires careful historical documentation. At this time, it is fair to say that nuclear commanders do not have a way to comprehend this level of interactive complexity with many random, non-linear, and invisible effects on the information sent and received by adversarial states via their NC3 operations.[59]
What can be said with confidence is that nuclear-armed states have had nuclear near-misses due to near loss of control or communication failures implicating NC3 with distressing regularity. One recent tally of such near nuclear-use incidents shows nine such incidents before 1987 (see Figure 11). To these may be added at least three other incidents between 1958 and 1987 all in this region, namely: Quemoy Matsu Crisis, 1958; Okinawan Missile Firing incident, October 1962; and DMZ “poplar tree” crisis, August 1976.[60] In all these cases, nuclear weapons were directly involved in military operations relating to the conflicts. for a total of twelve over four decades, or about one incident per four years. We also have no experience with nuclear war involving more than one nuclear-armed state. Unfortunately, the odds are that the NC3 systems will fail during a nuclear war as command posts and communication links are knocked out, and its negative controls fail and positive controls are overcome by false positive errors in the early warning system.[61]
Figure 11: Incidents of Near-Nuclear Use
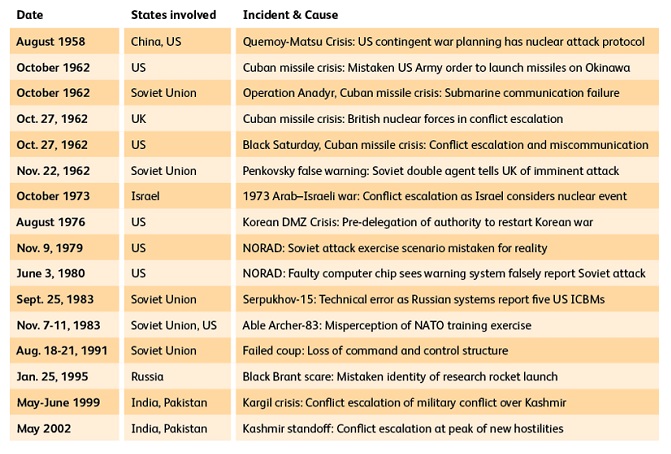
Source: P. Lewis et al, “Too Close for Comfort: Cases of Near Nuclear Use and Options for Policy” Royal Institute of International Affairs, April 2014; updated for Asian incidents in P. Hayes, “Nuclear Command Control and Communications in the Asia-Pacific,” Global Asia, 16:2, June, 2021, at: https://www.globalasia.org/v16no2/cover/nuclear-command-control-and-communications-in-the-asia-pacific_peter-hayes
Pandemic-Nuclear Nexus and NC3
The pandemic may destabilize a nuclear-prone conflict by incapacitating the supreme nuclear commander or commanders who have to issue nuclear strike orders, creating uncertainty as to who’s in charge, how to handle nuclear mistakes (errors, accidents, technological failures, entanglement with conventional operations gone awry), and opening a brief opportunity for a first strike at a time when the “infected” state may not be able to retaliate efficiently or at all due to leadership confusion.
In the American case, the US military decided to activate its backup command center deep inside Cheyenne Mountain in Colorado on March 19, 2020, in case the primary command post became infected.[62] Missile crews normally sent into silos for 48 hours found themselves spending two weeks underground.[63] The total personnel cost of quarantining and spatially distancing for NC3 duties increased dramatically. The airborne E6 command posts, for example, split their personnel into separate shifts to reduce infection risk.[64] Because many of the crews working on NC3 messaging and cyber support of these squadrons are older, they are in the high-risk category and vulnerable to infection.[65]
The UK prime minister and the US president have already been hospitalized for coronavirus. In the UK case, the prime minister was intubated and passed his powers to the Foreign Secretary Dominic Raab. Whether this included his nuclear strike authority is unknown.[66] In Trump’s case, he kept all his powers and appeared to be manic and behaved bizarrely and irrationally during and after his hospitalization, possibly due to the effects of the drug cocktail treatment he demanded.[67] KJU also disappeared at this time, sparking speculation that he was in isolation to avoid infection on a vessel at Wonsan.[68] Clearly, the pandemic has a direct impact on the nuclear command and control function of NC3.
The importance of NC3 likely increased during the pandemic because of its outsized role in the perception of the credibility of the threat to use nuclear weapons in a crisis. In some nuclear-laden conflicts, the pandemic might induce a state actor to use the pandemic as a cover for political or military provocations in the belief that the adversary is distracted and partly disabled by the pandemic, increasing the risk of war in a nuclear-prone conflict. At the same time, it may lead nuclear armed states to increase the isolation and sanctions against a nuclear adversary making it even harder to stop the pandemic in that state, in turn creating a pandemic reservoir and transmission risk back to the nuclear armed state and/or its allies. The DPRK is a case in point.[69]
Conversely, if the pandemic ravages or disables conventional forces, it might lead a nuclear armed state to increase its use of nuclear threat to substitute for its self-perceived loss of conventional deterrence credibility, using rhetoric or other signalling such as deployments or testing to send this message. The United States is a case in point.[70]
The pandemic may directly reduce the credibility of nuclear extended deterrence when the allied state and population see the great power’s inability to manage the pandemic;[71] and, indirectly, because it may introduce an infection risk associated with rotating and forward-deployed power projection forces in a host allied or umbrella state. Australia is a case in point.[72]
In principle, the common threat of the pandemic might induce nuclear-armed states to reduce the tension in a nuclear-prone conflict and thereby the risk of nuclear war. It may cause nuclear adversaries or their umbrella states to seek to resolve conflicts in a cooperative and collaborative manner by creating habits of communication, engagement, and mutual learning that come into play in the nuclear-military sphere. An example might be military-military cooperation to control pandemic transmission by continuing convergence of criminal-terrorist non-state actors, for example, people trafficking as a transmission vector, or to ensure that a new pathogen is not a bioweapon.
To date, however, the pandemic has increased the isolation of some nuclear-armed states and provided a text-book case of great power competition and failure to cooperate to overcome the pandemic. Borders have slammed shut, trade shut down, and budgets blown out, creating enormous pressure to focus on immediate domestic priorities. Foreign policies are markedly more nationalistic. Dependence on nuclear weapons may increase to buttress a global re-spatialization of all dimensions of human interaction at all levels by states to manage pandemics. The impact of nuclear threats on leaders may make it or even impossible to achieve the kind of concert at a global level needed to respond to and to administer an effective vaccine at a global level, making it harder and even impossible to revert to pre-pandemic international relations. The result is that some states may proliferate their own nuclear weapons, further reinforcing the spiral of conflicts contained by nuclear threat, with cascading effects on the risk of nuclear war.
How NC3 plays out in each of these dynamics is impossible to predict in such a contradictory and turbulent period of transition.
NC3: WHAT IS TO BE DONE?
Currently, there are no international standards or norms that are specific to NC3 operations—the sole exception being the clause in US-Soviet/Russian nuclear arms treaties that proscribes interference with national technical means,[73] which is an integral part of NC3. Of course, all international humanitarian laws and related treaties that apply in general to the use of nuclear weapons apply to NC3 personnel, military and civilian.[74]
Whether NC3 operations in the nine nuclear weapons states are sufficiently rigorous, robust, and secure to ensure that nuclear weapons will not be used except in extremis—defined by the International Court of Justice’s 1996 ruling on the legality of nuclear weapons was when the existence of the state itself is threatened—is doubtful. There is some evidence that at least lip service is paid to how international law shapes nuclear use options in the various elements that constitute NC3 including all instructions, orders, guidance, training, domestic laws, and the overall design of the NC3 architecture to ensure negative controls and avoid mistaken nuclear strikes. The standard for operating NC3 that is consistent with international law may be so high as impossible to achieve, in which case systematic tests against the legal criteria, similar to those conducted to ascertain the reliability with which nuclear weapons can be delivered, would rule out deployment.[75]
It is urgent, therefore, to commence dialogue within and between nuclear-armed states on the legal standards against which NC3 must be measured and transparency with regard to the achievement of minimum levels of NC3 performance.
It is inconceivable in the current international context, especially during pandemics, to negotiate international and legally binding agreements on NC3. Nonetheless, it is possible to start the ball rolling with dialogues within and between nuclear weapons states, and with nuclear umbrella states that host NC3 facilities, on the norms and best practices that should define the NC3 system of all nuclear-armed states, at minimum. Similar to the codification of the norms and best practices undertaken in the 2002 Hague Code on Missile Proliferation,[76] states could develop and commit to a global NC3 code of conduct. Some of the norms and best practices that might be included in such a code are listed in Table 3 below.
Table 3: GLOBAL NC3 CODE OF CONDUCT
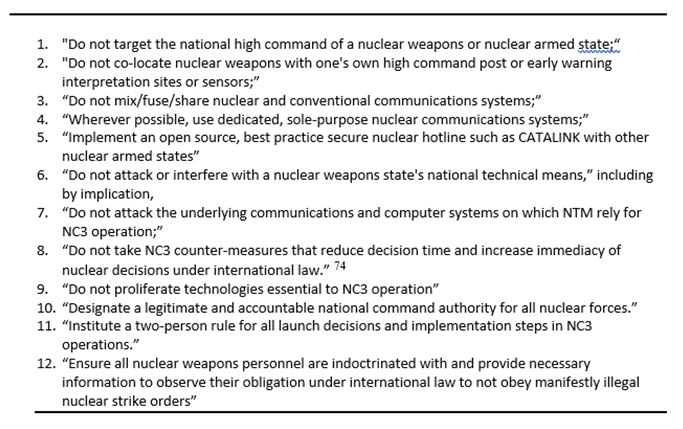
Any of these NC3 “commandments” might form the basis for a dialogue in Asia Pacific. The proposal to establish modern nuclear hotlines is an urgent risk reduction measure given the complexity of interacting NC3 systems today. This is a measure that might be supported not only by nuclear-armed and nuclear-umbrella states, by also by non-nuclear states that are not prohibition states, building a broad coalition around an international consensus that responsible nuclear commanders must be able to communicate at all times with nuclear-armed adversaries. Non-nuclear states that are also prohibition states might join a similar coalition pressing for nuclear-armed states to sign up to not targeting the high command of a nuclear-armed state as they ar-e able to do so with conventional weapons, thereby potentially destabilizing a conflict dyad based on nuclear threat.
There are also options for prohibition states that have ratified the Nuclear Weapons Prohibition Treaty, which proscribes hosting of NC3 facilities to exert leverage. They can enhance their normative and legal power by committing to hold nuclear commanders to account for the effects of any use of a nuclear weapon, or for its accidental use. One proposal is for prohibition states to not wait for a nuclear war to act on this commitment, but to create nuclear war crimes tribunals now to deter nuclear commanders from manipulating nuclear risk for political or military gain for any reason.[78]
They could also recognize and support (with sanctuary if necessary) “nuclear refuseniks” who are active-duty military and civilian personnel in an NC3 system who disobey manifestly illegal nuclear operations and orders to fire nuclear weapons. Examples of such personnel are well documented in the United States and more recently, in the UK, and they likely exist in all nuclear-armed and nuclear umbrella states hosting NC3 facilities. Their moral leadership and ethical performance should be recognized and celebrated for what it is: the individual standing against the entire NC3 apparatus that is preparing to annihilate humanity or large chunks of it.
III. ENDNOTES
[1] P. Bracken, The Command of Strategic Forces, Dissertation, Yale University, 1982, p. 39.
[2] Ashton Carter, “Sources of Error and Uncertainty,” in A. Carter, J. Steinbruner, and C. Zraket, ed, Managing Nuclear Operations, The Brookings Institution, Washington DC, 1987, p. 635.
[3] For example, Fiona Cunningham reports that there is no open-source clear definition of “NC3” with Chinese characteristics, although there are various command and control concepts in the Chinese literature that relate to elements of NC3 as defined by the United States and NATO. See Fiona Cunningham, “Nuclear Command, Control, and Communications Systems of the People’s Republic Of China”, NAPSNet Special Reports, July 18, 2019, https://nautilus.org/napsnet/napsnet-special-reports/nuclear-command-control-and-communications-systems-of-the-peoples-republic-of-china/
[4] Termed C³1: Ashton B. Carter, “The Command and Control of Nuclear War,” Scientific American 252, 1 (Jan, 1985): 32-39, 32. Carter’s work on vulnerability was preceded by a seminal paper by D. Ball, Can nuclear war be controlled? Adelphi Papers, 1981, 21: 169, pp. 1-2, at: http://www.tandfonline.com/doi/abs/10.1080/05679328108457385
[5] US Department of Defense, Nuclear Matters Handbook, chapter 2, accessed October 3, 2020, at: https://www.acq.osd.mil/ncbdp/nm/nmhb/chapters/chapter2.htm
[6] US Department of Defense, Nuclear Matters Handbook, op cit.
[7] US Department of Defense, Nuclear Matters Handbook, op cit.
[8] US Department of Defense, Nuclear Matters Handbook, op cit.
[9] US Department of Defense, Nuclear Matters Handbook, op cit.
[10] US Air Force, “Air Force Nuclear Command, Control, and Communications (NC3), US Air Force Instruction 13-550, October 2, 2014, p.21, released under US FOIA request to Nautilus Institute.
[11] Jeffrey Larsen, “Nuclear Command, Control, and Communications: US Country Profile”, NAPSNet Special Reports, August 22, 2019, https://nautilus.org/napsnet/napsnet-special-reports/nuclear-command-control-and-communications-us-country-profile/
[12] Answer to Question 1 at: Nuclear Command, Control, and Communications System Operational Assessment Program, Solicitation Number: HC104710R4009, Agency: Defense Information Systems Agency, Office: Procurement Directorate Location: DITCO-NCR, August 4, 2010, at: https://www.fbo.gov/index?s=opportunity&mode=form&id=ca9ed977f427844fb095c1e170a579ee&tab=core&_cview=1
[13] S. Magnuson, “Exclusive: Interview with Gen. Robin Rand, Head of Air Force Global Strike Command,” National Defense Magazine, November 14, 2017, at: http://www.nationaldefensemagazine.org/articles/2017/11/14/global-strike-command-tackles-atrophying-nuclear-command-control-systems
[14] Presentation at NC3 and Global Stability, workshop, Stanford University, January 22-23, 2019. See Peter Hayes, Binoy Kampmark, Philip Reiner, Deborah Gordon, “SYNTHESIS REPORT–NC3 SYSTEMS AND STRATEGIC STABILITY: A GLOBAL OVERVIEW”, NAPSNet Special Reports, May 05, 2019, https://nautilus.org/napsnet/napsnet-special-reports/synthesis-report-nc3-systems-and-strategic-stability-a-global-overview/
[15] Jeffrey Larsen, “Nuclear Command, Control, and Communications: US Country Profile,” NAPSNet Special Reports, August 22, 2019, https://nautilus.org/napsnet/napsnet-special-reports/nuclear-command-control-and-communications-us-country-profile/
[16] Statement of The Honorable Ellen M. Lord Under Secretary of Defense for Acquisition and Sustainment Before the Strategic Forces Subcommittee Committee on Armed Services United States Senate U.S. Nuclear Weapons Policy, Programs, and Strategy in Review of the Defense Authorization Request for Fiscal Year 2020 and the Future Years Defense Program May 1, 2019, at: https://www.armed-services.senate.gov/download/lord_05-01-19
[17] At the NC3 Systems and Strategic Stability: A Global Overview workshop, January 22, 2019, under Chatham House Rule. A month later, General John Hyten stated in testimony that he “I really can’t effectively explain” why the NC3 systems works. In US Strategic Command, “U.S. Strategic Command and U.S. Northern Command SASC Testimony,” March 1, 2019, at:
[18] Leonid Ryabikhin, “Russia’s NC3 and Early Warning Systems”, NAPSNet Special Reports, July 11, 2019, https://nautilus.org/napsnet/napsnet-special-reports/russias-nc3-and-early-warning-systems/
[19] J. Trevithick, “Putin Reveals Existence Of New Nuclear Command Bunker, November 11, 2020, The War Zone, at: https://www.thedrive.com/the-war-zone/37569/putin-reveals-existence-of-new-nuclear-command-bunker-and-says-its-almost-complete?mkt_tok=eyJpIjoiWVRObE5tTmlPR00wTURCbCIsInQiOiI4eWhUa3E4d2x6amRaeVBOQnVlK0lrcEJRSTNlY1JidUhtVEZJU2xUSUU2T05vSm1HZTNEVmx0XC9uajE4MWpWSVwvM0ZuWjJSR2xQWHZWXC9jNEs3eUtGV3o1SVNOd2RcL3F1TlpcL2YyT3E3VVdKREl4ekI4YmNOaSs2ZTdubWlibU1EIn0%3D
[20] K. Lippold, U.S. and Soviet Strategic Command and Control: Implications for a Protracted Nuclear War, thesis, US Naval Postgraduate School, Monterey, March 1989, p.124, at: https://calhoun.nps.edu/handle/10945/26326
[21] K. Lippold, U.S. and Soviet Strategic Command and Control: Implications for a Protracted Nuclear War, thesis, US Naval Postgraduate School, Monterey, March 1989, p.124, at: https://calhoun.nps.edu/handle/10945/26326
[22] “Russia’s satellite nuclear warning system down until November,” The Moscow Times, June 30, 2015, at: https://www.themoscowtimes.com/2015/06/30/russias-satellite-nuclear-warning-system-down-until-november-a47799
[23] Sergei Boev, the lead designer, explained in 2015, “The system’s ground echelon…is a uniquely complicated technical system and malfunctions cannot be excluded. Here a lot depends on how the system’s various components interact with one another: the false alarms that can occur in one station must be quickly analyzed and verified by the command post.” In “Revealed: Russia’s ambitious new ICBM early warning system,” Sputnik News (19 August 2015, at: https://sputniknews.com/russia/201508191025927540-russia-nuclear-early-warning-system-development/
[24] This section draws on F. Cunningham, “Nuclear Command, Control, and Communications Systems of the People’s Republic Of China,” NAPSNet Special Reports, July 18, 2019, https://nautilus.org/napsnet/napsnet-special-reports/nuclear-command-control-and-communications-systems-of-the-peoples-republic-of-china/
[25] T. Zhao, Tides of Change: China’s Nuclear Ballistic Missile Submarines and Strategic Stability, Carnegie Endowment for International Peace, October 24, 2018 at: https://carnegietsinghua.org/2018/10/24/tides-of-change-china-s-nuclear-ballistic-missile-submarines-and-strategic-stability-pub-77490
[26] Ta-chen Cheng, “China’s nuclear command, control and operations,” International Relations of the Asia-Pacific, no 7, March 5, 2007 pp. 169-170, at: https://www.jstor.org/stable/26156651?seq=1. Stephen Polk states that as of early 2000s, China’s NC2 is located at three sites: in Beijing, at the Central Military Commission office in the Ministry of Defense, the General Staff Directorate hardened bunker in western Beijing where the PLA controls its nuclear forces and issues orders, and the Second Artillery now PLA Rocket Force headquarters nearby in Qinghe. S. Polk, “China’s Nuclear Command and Control,” in Lyle J. Goldstein, ed, with Andrew S. Erickson, China’s Nuclear Force Modernization, Newport Paper Twenty-two, Center for Naval Warfare Studies, 2005 at: https://digital-commons.usnwc.edu/cgi/viewcontent.cgi?article=1021&context=newport-papers
[27] S. Polk, op cit, p. 17.
[28] Cunningham, op cit.
[29] Ibid.
[30] This section relies on Myeongguk Cheon, “DPRK’S NC3 SYSTEM”, NAPSNet Special Reports, June 06, 2019, https://nautilus.org/napsnet/napsnet-special-reports/dprks-nc3-system/
[31] M.V. Ramana and Lauren J. Borja, “Command and Control of Nuclear Weapons in India”, NAPSNet Special Reports, August 01, 2019, https://nautilus.org/napsnet/napsnet-special-reports/command-and-control-of-nuclear-weapons-in-india/
[32] Rakesh Kumar, Indian Nuclear Command and Control Dilemma, thesis, Naval Postgraduate School, Monterey, September 2006, pp. 31-32 at: https://calhoun.nps.edu/handle/10945/2639?show=full
[33] S. Smith, Assessing the Risk of Inadvertent Nuclear War Between India and Pakistan, thesis, Naval Postgraduate School, Monterey, December 2002, p. 47, at: https://calhoun.nps.edu/handle/10945/3272
[34] R. White, “Command and Control of India’s Nuclear Forces,” TheNonproliferation Review, 21:3-4, 2014, p. 270, at: https://www.tandfonline.com/doi/abs/10.1080/10736700.2014.1072994?tab=permissions&scroll=top
[35] S. Saran, “Is India’s Nuclear Deterrent Credible?” India Habitat Centre, New Delhi, April 24, 2013, p. 11, at: http://krepon.armscontrolwonk.com/files/2013/05/Final-Is-Indias-Nuclear-Deterrent-Credible-rev1-2-1-3.pdf
[36] A. Ahmed, “Indian Nuclear Command and Control,” Indian Defence Review, part 2, July 13, 2011, at: http://www.indiandefencereview.com/spotlights/indian-nuclear-command-and-control–ii/
[37] A. Ahmed, “Indian Nuclear Command and Control,” Indian Defence Review, part 1, July 12, 2011, p. 2, at: http://www.indiandefencereview.com/spotlights/indian-nuclear-command-and-control-i/
[38] “VLF Transmitting Station Commissioned at Tamil Nadu,” Indian Navy, Press Release, no date, at: https://www.indiannavy.nic.in/content/vlf-transmitting-station-commissioned-tamil-nadu
[39] K. Mahesh, “Navy to reach ships and subs from Pudur,” Times of India, December 27, 2017, at: http://timesofindia.indiatimes.com/articleshow/62261258.cms?utm_source=contentofinterest&utm_medium=text&utm_campaign=cppst
[40] J. Yogesh, F. O’Donnell, “India and Nuclear Asia: Forces, Doctrine, and Dangers,” Georgetown University Press, 2019, Kindle Edition, p. 55.
[41] Feroz Hassan Khan, “Nuclear Command, Control and Communications (NC3): The Case of Pakistan”, NAPSNet Special Reports, September 26, 2019, https://nautilus.org/napsnet/napsnet-special-reports/nuclear-command-control-and-communications-nc3-the-case-of-pakistan/
[42] S. Gregory, “Nuclear Command and Control in Pakistan,” Defense & Security Analysis, 23:3, 315-330, 2007, at: https://doi.org/10.1080/14751790701573907
[43] G. Mujaddid, “The Next Decade of Nuclear Unlearning: Command and Control and Management of Pakistan’s Nuclear Weapons,” in F. Khan et al, edited, Nuclear Learning in South Asia: The Next Decade, Naval Postgraduate School, Monterey, June 2014 at: https://calhoun.nps.edu/handle/10945/45142
[44] U. Ansari, “Pakistan Unveils VLF Submarine Communications Facility,” Defense News, Nov 16, 2016, at: https://www.defensenews.com/naval/2016/11/16/pakistan-unveils-vlf-submarine-communications-facility/
[45] F.H. Khan, Going Tactical: Pakistan’s Nuclear Posture and Implications for Stability, IFRI Security Studies Center, Proliferation Papers 53, Paris, 2015, at: https://www.ifri.org/sites/default/files/atoms/files/pp53khan_0.pdf
[46] J. Yogesh, F. O’Donnell, India and Nuclear Asia, op cit, p. 320.
[47] Ashton Carter, “Sources of Error and Uncertainty,” in A. Carter, J. Steinbruner, and C. Zraket, ed, Managing Nuclear Operations, The Brookings Institution, 1987, pp. 611-640.
[48] Scott Sagan, The Limits of Safety, Organizations, Accidents, and Nuclear Weapons, Princeton, New Jersey 1993
[49] P. Bracken, The Command of Strategic Forces, Dissertation, Yale University, 1982, p. 39.
[50] Gary A. Ackerman, “The Non-State Dimension of Nuclear Command, Control and Communications,” NAPSNet Special Reports, August 29, 2019, https://nautilus.org/napsnet/napsnet-special-reports/the-non-state-dimension-of-nuclear-command-control-and-communications/
[51] See the account of the coup and disputes related thereto in Benoît Pelopidas, “France: Nuclear Command, Control, and Communications,” NAPSNet Special Reports, June 10, 2019, https://nautilus.org/napsnet/napsnet-special-reports/france-nuclear-command-control-and-communications/
[52] M. Dobbs, “During the Soviet Coup, Who Held Nuclear Control? Gorbachev Lost Command, Probers Say,” New York Times, August 23, 1992, at: https://www.washingtonpost.com/archive/politics/1992/08/23/during-the-soviet-coup-who-held-nuclear-control-gorbachev-lost-command-probers-say/a4732610-679e-4f6e-be69-f0cf3f9eba85/ and C. Bohlen, “Gorbachev Lost Nuclear Control, Russians Report,” New York Times, August 23, 1992, at: https://www.nytimes.com/1992/08/23/world/gorbachev-lost-nuclear-control-russians-report.html
[53] Elsa B. Kania, “Emerging Technologies, Emerging Challenges—The Potential Employment of New Technologies in Future PLA NC3”, NAPSNet Special Reports, September 05, 2019, https://nautilus.org/napsnet/napsnet-special-reports/emerging-technologies-in-future-pla-nuclear-command-control-and-communications/ and Peter Hayes, “Nuclear Command-and-Control in the Quantum Era”, NAPSNet Blue Peter, March 29, 2018, https://nautilus.org/napsnet/nuclear-command-and-control-in-the-quantum-era/
[54] See Nautilus Institute, Technology for Global Security, Preventive Defense Project, “Social Media Storms and Nuclear Early Warning Systems: A Deep Dive and Speed Scenarios Workshop Report,” NAPSNet Special Reports, January 08, 2019, https://nautilus.org/napsnet/napsnet-special-reports/social-media-storms-and-nuclear-early-warning-systems-a-deep-dive-and-speed-scenarios-workshop-report/ and H. Williams and A. Drew Escalation by Tweet: Managing the New Nuclear Diplomacy, Centre for Science & Security Studies, Kings College, London, July 15, 2020, at: https://www.kcl.ac.uk/csss/assets/10957%E2%80%A2twitterconflictreport-15july.pdf
[55] A. Wellerstein, “NC3 Decision Making,” op cit.
[56] James Acton, “For Better or For Worse: The Future of C3I Entanglement”, NAPSNet Special Reports, November 21, 2019, https://nautilus.org/napsnet/napsnet-special-reports/for-better-or-for-worse-the-future-of-c3i-entanglement/
[57] C. Perrow, Complex Organizations: A Critical Essay, Random House, New York, 1986, p. 148.
[58] This account treats Israel, the UK, and France as outside the Asia-Pacific region, and it also omits US nuclear umbrella allies in NATO and Asia Pacific (Japan, the ROK, Australia) although they may be targeted due to their NC3 facility hosting roles to support US nuclear forces.
[59] For example, in 2013, the U.S Air Force and the U.S. Strategic Command began to use a new format for their EAMs, just as the crisis with North Korea heated up with US strategic bombers on the move. See Peter Hayes, “Continuation of Policy With other Means: Ensuring that the March-April 2017 US-ROK Military Exercises Do Not Increase the Risk of War”, NAPSNet Special Reports, March 07, 2017, https://nautilus.org/napsnet/napsnet-special-reports/continuation-of-policy-with-other-means-ensuring-that-the-march-april-2017-us-rok-military-exercises-do-not-increase-the-risk-of-war/
[60] For the Taiwan incident, see P. Hayes et al, American Lake, Nuclear Peril in the Pacific, Penguin, Melbourne 1987; for the August 1976 DMZ incident, see P. Hayes, Pacific Powderkeg, American Nuclear Dilemmas in Korea, Lexington Books, 1991, at: http://nautilus.org/wp-content/uploads/2011/04/PacificPowderkegbyPeterHayes.pdf; for the 1962 Okinawa incident, see A. Tovish, “The Okinawa Missiles of October.” Bulletin of Atomic Scientists, October 25, 2105 at: http://thebulletin.org/okinawa-missiles-october8826 and T. Tritten, “Cold War Missileers Refute Okinawa Near-Launch.” Stars and Stripes, December 23, 2015 at: http://www.stripes.com/news/special-reports/features/cold-war-missileersrefute-okinawa-near-launch-1.385439
[61] See B. Blair, S. Philippe, S. Weiner, “Right Of Launch: Command And Control Vulnerabilities After A Limited Nuclear Strike,” November 20, 2020, at: https://warontherocks.com/2020/11/right-of-launch-command-and-control-vulnerabilities-after-a-limited-nuclear-strike/
[62] B. Bender, “How the nuclear force dodged the coronavirus, Preparing for doomsday has its benefits in a pandemic,” Politico, April 23, 2020, at:
https://www.politico.com/news/2020/04/23/nuclear-force-coronavirus-205230
[63] A. Capaccio, “Nuclear-Missile Crews Pull Longer Tours in Virus-Hit Air Force,” Bloomberg, April 15, 2020, at: https://www.bloomberg.com/news/articles/2020-04-15/nuclear-missile-crews-pull-longer-tours-in-virus-hit-air-force
[64] Vanden Brook, “Top priority for nuclear forces amid coronavirus pandemic: stay healthy,” USA Today, April 20, 2020, at: https://www.usatoday.com/story/news/politics/2020/04/20/coronavirus-has-missile-crews-high-alert-military-risks-play-out/5154223002/
[65] J. F. Rossi, “The US Air Force is adapting to the pandemic to keep missile systems running” C4ISRNet, March 30, 2020, at: https://www.c4isrnet.com/opinion/2020/03/30/the-us-air-force-is-adapting-to-the-pandemic-to-keep-missile-systems-running/?utm_source=Sailthru&utm_medium=email&utm_campaign=C4ISRNET%20Daily%20Brief%203.31&utm_term=Editorial%20-%20Daily%20Brief
[66] “Who has the UK nuclear button while Johnson is ill? No comment,” Reuters, April 7, 2020, at: https://uk.reuters.com/article/health-coronavirus-britain-nuclear/who-has-the-uk-nuclear-button-while-johnson-is-ill-no-comment-idUSL8N2BV1Z5 and “Trump Departs for Hospital After Positive Test,” New York Times, October 2, 2020, at: https://www.nytimes.com/video/us/politics/100000007375894/trump-walter-reed-coronavirus.html
[67] S. Benen, “White House reportedly wonders about meds affecting Trump’s behavior, What does it say about a person when it’s hard to tell the difference between his usual persona and the one he displays while on mood-altering medications?” October 7, 2020, at: https://www.msnbc.com/rachel-maddow-show/white-house-reportedly-wonders-about-meds-affecting-trump-s-behavior-n1242392 and B. Levin, “Report: Some People Thinking a Drug-Addled Maniac (Donald Trump) Shouldn’t Be in Charge of the Nuclear Codes, Trump’s behavior since going on steroids has revived concern he could unilaterally start a nuclear war,” Vanity Fair, October 12, 2020 at: https://www.vanityfair.com/news/2020/10/donald-trump-steroids-nuclear-war
[68] “Kim Jong-un could be sheltering from Covid-19 pandemic, say US and Seoul,” The Guardian, April 29, 2020, at:
[69] J. Yun et al, North Korea: Coronavirus, Missiles and Diplomacy, The COVID-19 crisis has the potential to ease tensions between Washington and Pyongyang—but it’s more likely negotiations will remain deadlocked,” US Institute of Peace, April 7, 2020 at: https://www.usip.org/publications/2020/04/north-korea-coronavirus-missiles-and-diplomacy
[70] S.Y. Choi “US bombers conduct drill over Korean Peninsula in show of force,” Korea Herald, August 19, 2020, at: http://www.koreaherald.com/view.php?ud=20200819000614
[71] Allan Behm, “Extended Deterrence and Extended Nuclear Deterrence in a Pandemic World”, NAPSNet Special Reports, October 15, 2020, https://nautilus.org/napsnet/napsnet-special-reports/extended-deterrence-and-extended-nuclear-deterrence-in-a-pandemic-world/
[72] Darwin incident.
[73] The concept of non-interference with national technical means of verification first appeared in the Strategic Arms Limitation Talks (SALT) I Treaty of 1972. It was taken over into the Intermediate Range Nuclear Forces (INF) Treaty, which is of indefinite duration, and into the Treaty on the Reduction and Limitation of Strategic Offensive Arms (START I), which has been extended to 2009. The intent of this noninterference measure is to preserve from attack or interference technical means of verifying treaty compliance, including space-orbiting means. It would be a violation of the provisions on noninterference with national means of verification in the INF and START I treaties to use weapons against any early warning, imaging, or intelligence satellite and, by extension, against any ocean surveillance, signals, intelligence, or communications satellite of the United States or Russia. This obligation was made multilateral in the Conventional Forces in Europe (CFE) Treaty, which has 30 NATO and East European participants and is of unlimited duration. The best overview of this non-interference norm is: D. Koplow, “An Inference about Interference: A Surprising Application of Existing International Law to Inhibit Anti-Satellite Weapons,” Journal of International Law, 35:3, 2014, pp. 737-826, at: http://scholarship.law.upenn.edu/cgi/viewcontent.cgi?article=1868&context=jil
[74] Bill Boothby and Wolff Heintschel von Heinegg tackle the legality of NC3 in their Nuclear Weapons Law – Where Are We Now? forthcoming, Cambridge University Press, 2021.
[75] Nuclear command and control is measured in US tests of the operational reliability of its nuclear forces. The methodology is explained as follows:
“Command and Control Procedures (CCP). In order to quantify the reliability of CCP from message transmission to execution, Services will provide CCP metrics that estimate the probability crews will receive a valid EAM [Emergency Action Message] and the probability they perform all necessary actions within the system’s required time limit to commit a nuclear weapon.
a) The CCP timeline is from message transmission to weapon release. The timeline includes the following: message transmission, receipt, decoding validating, authentication and verification procedures, and Permissive Action Link (PAL) operations.” Enclosure B, p. BII, US Strategic Command Instruction, “Guidelines for Nuclear Weapon System Operational Testing and Reporting,” SI 526-01, June 30, 2020, released under US Freedom of Information Act request to Nautilus Institute, November 20, 202, to be published.
[76] The HCOC is a 2002 voluntary, non-binding agreement with signatories now totaling more than 135 states parties. It involves annual reporting of ballistic missile testing and provisions for pre-launch notification. The code’s effectiveness could be reinforced and augmented in a variety of ways—for example, by expanding the code’s membership, strengthening compliance mechanisms, and adding cruise missiles, hypersonic vehicles, and even missile defense to the code’s purview. The code could also be revised to incorporate measures regarding transparency, confidence building, and crisis management—measures that some states have already implemented via bilateral agreements. The text is found on the Hague Code of Conduct against Ballistic Missile Proliferation (HCOC) secretariat website at: http://www.hcoc.at/?tab=what_is_hcoc&page=text_of_the_hcoc
Other codes from parallel fields may be salient to a global NC3 Code of Conduct. Codes of conduct are ubiquitous in international relations and law and present many advantages relative to treaty-based international law. Codes cover a wide spectrum from labor, human rights, and environmental concerns to international financing. For an overview of such codes, see J. Friedrich, “Codes of Conduct,” in Max Planck encyclopedia of public international law (0-edited R. Wolfrum, Oxford University Press, 2008, updated October 2010, at: http://opil.ouplaw.com.ezproxy1.library.usyd.edu.au/view/10.1093/law:epil/9780199231690/law-9780199231690-e1379?rskey=oWSI5g&result=1&prd=OPIL
The Stimson Center’s draft Code for Responsible Space-Faring Nations is another model for drafting a global NC3 Code, see https://www.stimson.org/model-code-of-conduct-for-responsible-space-faring-nations
Also salient is the proposed Woomera Manual on the International Law of Military Space Operations on which see https://law.adelaide.edu.au/woomera/system/files/docs/Woomera%20Manual.pdf and the existing Tallin manual, see International Group of Experts, Tallinn Manual 2.0 on the International Law Applicable to Cyber Operations, Cambridge University Press, February 2017, at: http://www.cambridge.org/us/academic/subjects/law/humanitarian-law/tallinn-manual-20-international-law-applicable-cyber-operations-2nd-edition?format=PB
[77] By causing another state to shorten its decision times, for example, by positioning forces in a manner that compresses time from launch from time to detonation, a state may increase immediacy, thereby justifying its adversary’s decision to strike first. “All else being equal, immediacy is essentially what separates self-defence that is lawful under jus ad bellum from armed reprisals that are generally considered unlawful under jus ad bellum.” Nobuo Hayashi, “nuclear weapons and requirements of necessity and proportionality ad bellum,” in Gro Nystuen, Stuart Casey-Maslen, Annie Golden Bersagel, Nuclear Weapons under International Law (Kindle Locations 807-808) Cambridge University Press. Kindle Edition, 2014
[78] See. A. Colangelo & P. Hayes An International Tribunal for the Use of Nuclear Weapons, Journal for Peace and Nuclear Disarmament, June 2019, pp. 219-252, at: https://www.tandfonline.com/doi/full/10.1080/25751654.2019.1624248?tab=permissions&scroll=top
IV. NAUTILUS INVITES YOUR RESPONSE
The Nautilus Asia Peace and Security Network invites your responses to this report. Please send responses to: nautilus@nautilus.org. Responses will be considered for redistribution to the network only if they include the author’s name, affiliation, and explicit consent.


