RECNA-NAGASAKI UNIVERSITY, ASIA PACIFIC LEADERSHIP NETWORK, NAUTILUS INSTITUTE
JANUARY 28 2022
I. INTRODUCTION
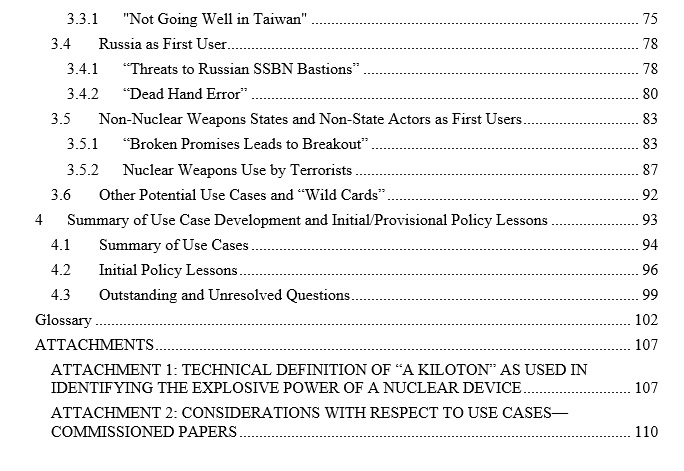
This report presents the results of year 1 of the Project on Reducing the Risk of Nuclear Weapons Use in Northeast Asia. In it, 21 plausible cases of first use of nuclear weapons involving the Korean peninsula. Each use case considers “Triggering Events and First Use,” “How the Conflict Evolves,” “Use Case Consequences,” and “Use Case Uncertainties, Ultimate Outcome, and Policy Lessons.”
“Let Nagasaki be the Last!” therefore must be the goal of nuclear security policymakers.
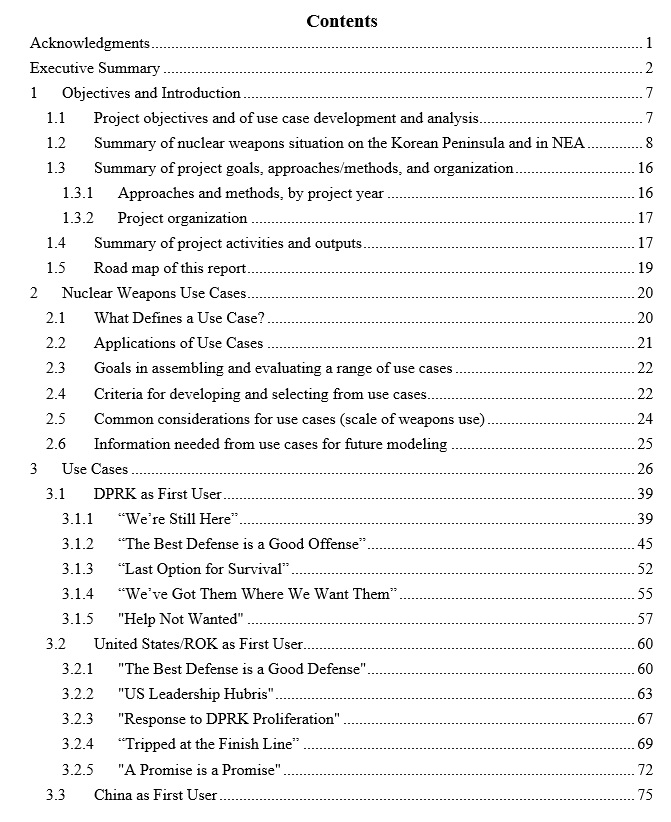
This posting provides only the Executive Summary and Table of Contents. The full report may be downloaded in PDF format [3MB] here
The Executive Summary in Japanese is here, in Chinese here, in Korean here
The report was prepared by primary author David F. von Hippel, with contributions from NU-NEA Project Staff and its Steering Committee: Peter Hayes, Shatabhisha Shetty, Tatsujiro Suzuki, Fumihiko Yoshida, Michiru Nishida, Eva Lisowski, and Steve Freedkin with copyediting by Maureen Jerrett.
This report is a part of a joint project on Reducing the Risk of Nuclear Weapon Use in Northeast Asia (NU-NEA) and has been cross-posted by the Asia Pacific Leadership Network here, and the Research Center for Nuclear Weapons Abolition (RECNA), and the Panel on Peace and Security of North East Asia (PSNA) here
The views expressed in this report do not necessarily reflect the official policy or position of the Nautilus Institute. Readers should note that Nautilus seeks a diversity of views and opinions on significant topics in order to identify common ground.
This report is published under a 4.0 International Creative Commons License the terms of which are found here.
Acknowledgement: The NU-NEA project is funded by Nagasaki University and the John D. and Catherine T. MacArthur Foundation.
Banner image: Sophia Mauro for Nautilus Institute.
II. NAPSNET SPECIAL REPORT BY RECNA-NAGASAKI UNIVERSITY, ASIA PACIFIC LEADERSHIP NETWORK, NAUTILUS INSTITUTE
POSSIBLE NUCLEAR USE CASES IN NORTHEAST ASIA: IMPLICATIONS FOR REDUCING NUCLEAR RISK
JANUARY 28 2022
Executive Summary
The bombings of Hiroshima and Nagasaki, Japan, in 1945 remain the only instances in history of nuclear weapons detonation in a conflict. In the three-quarters-of-a-century since, nuclear weapons have been “used” primarily as tools of deterrence or coercion—deterring conventional and nuclear attacks on the nations that possess them and on the allies of those nations and coercing other nations against mounting attacks. During that interval there have also been many documented instances, and probably many that remain state secrets, when nuclear weapons use was narrowly averted, sometimes by the bravery of someone in the nuclear chain of command, and sometimes, just by luck.
Any detonation of nuclear weapons in a conflict today (or in the years to come) risks absolutely unacceptable consequences, no matter how “limited” the nuclear exchange is or will be. The premise of this report is that it is crucial to understand a range of possible nuclear weapons “use cases”—the detonation of nuclear weapons at or near the earth’s surface in a conflict situation—to demonstrate the impacts of such use and to spur the development of policy options that can be deployed to reduce the potential for nuclear war in the future. The fact that these cases are posited here does not mean they are likely; it simply means they are plausible. Although some of the use cases do include only limited use, and in one case, failed use, of nuclear weapons, and lead, ultimately, to a meeting of the minds between nuclear-armed opponents and the eventual reduction of the risk of nuclear war, none of these use cases are in any way desirable in and of themselves, and all possible efforts should be made to avoid any nuclear weapons use. “Let Nagasaki be the Last!” must therefore be the goal of policymakers in international security.
The nuclear use cases posited in this Report span a range of cases, with a range of ultimate outcomes. In one case, a nuclear detonation is attempted but is not successful, and the adversary that is the recipient of the attack exercises sufficient restraint that no counterattack with nuclear weapons occurs. A variety of cases are provided where conflict involves a nuclear weapons detonation, in most cases followed by a nuclear counter-attack in which diplomacy results in the exchange being “limited” to a few targets. In some of the cases described it is hard to see how a conflict would result in anything short of global (or near-global) nuclear war.
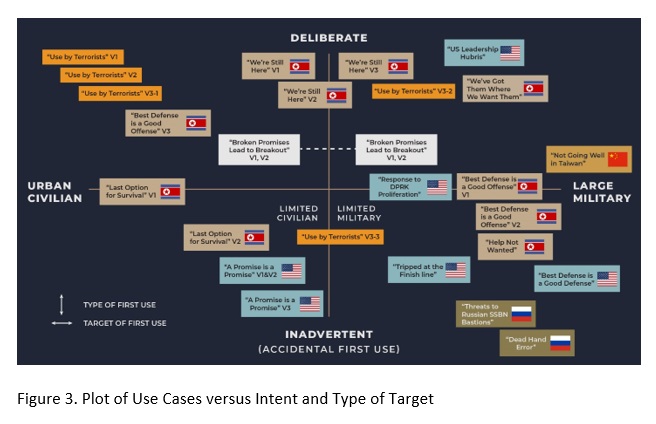
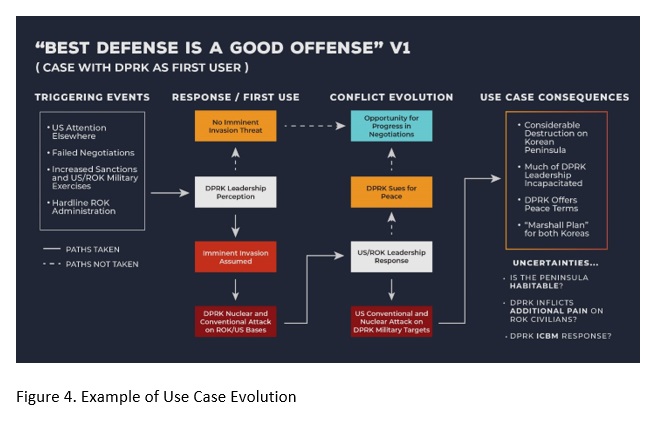
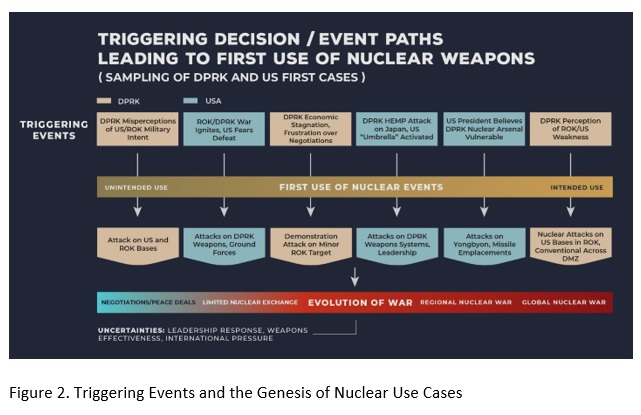
In the use cases presented, the elements of use cases considered are “Triggering Events and First Use,” “How the Conflict Evolves,” “Use Case Consequences,” and “Use Case Uncertainties, Ultimate Outcome, and Policy Lessons.” The use cases also span the continuum from “unintended” use, in which a state or non-state actor, for example, had not planned to use nuclear weapons but does so due to an accident and/or a misperception of an adversary’s intentions, to “intended” or “deliberate” use, when a party uses nuclear weapons for coercion or to gain advantage in a planned invasion. The use cases posit more numerous first use options for the DPRK and the United States as these are the principal antagonists on the Korean Peninsula, which has for many years been a primary, but hardly the only, locus of conflict in Northeast Asia. There are, however, additional first use cases that could be devised for China, and to an arguably lesser extent, Russia, and other actors.
Some of the similarities between use cases include:
- Many of the use cases involve first use in which one adversary misinterprets the actions of another.
- Many of the use cases turn on the personality of a leader and how he or she responds to a crisis involving nuclear weapons.
- Many of the use cases occur when one or more of the adversaries, or at least the leadership of same, are distracted by other issues, including domestic issues and issues abroad.
- Many of the use cases involve lack of communications, or lack of timely or clear communication between rivals and, in many cases, between allies, or even between those responsible for operating the assets of a single military.
- Many of the cases include key decision points where either escalation or de-escalation of a conflict is possible, based on the choices (or failures to choose) of military and civilian leaders at those moments.
- Many of the cases may involve large uncertainties about the outcome of the nuclear conflicts. It is difficult to foresee what would happen once a nuclear weapon is used, and nuclear use may escalate to uncontrollable nuclear conflict regardless of what decision makers want.
Key differences between use cases include:
- Although many use cases use similar delivery systems—dictated in part by the distance between adversaries as well as their arsenals—some use very different means of moving nuclear weapons to targets and thus require different sorts of policy approaches to reduce the threat of nuclear use.
- The nuclear arsenals that potential adversaries have, at this point, differ substantially in both quantity and quality, which colors the decisions to use or not use nuclear weapons.
- The nuclear weapons arsenals of the potential adversaries, and the technologies that can be used to deliver them, are not static; security challenges a few years from now may be addressed by very different weapons than are currently used.
- The adoption, or rejection, of opportunities for stopping conflict through negotiation. Different approaches to negotiation may produce significantly different outcomes to nuclear conflicts, although the effectiveness of negotiation can also vary widely.
Initial policy lessons from these use cases—to be revised and augmented based on analysis to be carried out in future years of the NU-NEA project—include:
- The need for continuously trusted and reliable open lines of communications between adversaries at multiple levels.
- To improve mutual trust and encourage transparency and consistency in describing the extent and operation of military alliances.
- Seek to separate as much as possible the operation of international relations from domestic political concerns, particularly (but hardly exclusively) in nations where leadership changes are frequent.
- Seek to insulate the operations of nuclear weapons from the personal or political vagaries of national leaders, possibly by strengthening oversight on the use of nuclear weapons.
- Seek to fully brief leaders, military and otherwise, regarding what is known, what is not known, and what is possible about the goals, concerns, and emphases of adversaries so as to allow leaders to better understand and identify, to the extent possible given typically substantial uncertainties, the ways in which opposing leaders might react in situations of stress.
- Exercise patience, and adjust expectations for results, in international negotiations, particularly those involving the DPRK.
- Equip nuclear weapons systems with redundant command and control mechanisms that help to assure that a nuclear weapon can never be launched without adequate authority and oversight.
- Work toward insulating key systems (electric power and communications among them) from high-altitude electromagnetic pulse (HEMP) bursts, and/or develop robust back-up arrangements designed to keep those systems running.
- Anticipate that potential breakdowns in communication in the nuclear command and control will occur, whether because of, for example, a HEMP detonation or cyberattack, or because of natural disasters such as earthquakes or severe “solar storms” and assure that commanders in possession/control of nuclear weapons have clear orders as to what to do in those instances.
- Encourage all nuclear weapon states to adopt a “No-first-Use” declaration policy as a step toward substantially reducing the risk of nuclear war. The declared nuclear weapons states (NWS) in the region should endorse such policies.
III. NAUTILUS INVITES YOUR RESPONSE
The Nautilus Asia Peace and Security Network invites your responses to this report. Please send responses to: nautilus@nautilus.org. Responses will be considered for redistribution to the network only if they include the author’s name, affiliation, and explicit consent


