JEFFREY LARSEN
AUGUST 22, 2019
I. INTRODUCTION
In this essay, Jeffrey Larsen reviews the legacy NC3 system of the United States now in the midst of a sea-change. He concludes: “The need to ensure robust existing capabilities for the current system, plus the desire to create a new system that is more than a simple modernization of existing capabilities, in a world facing more diverse threats, all while harnessing the value-added of new technologies, means that the NC3 system twenty years hence may bear little resemblance to its current arrangement.”
Jeffrey Larsen is president of Larsen Consulting Group.
Acknowledgments: The workshop was funded by the John D. and Catherine T. MacArthur Foundation.
This report is published simultaneously here by Technology for Global Security and here by Nautilus Institute and is published under a 4.0 International Creative Commons License the terms of which are found here.
The views expressed in this report do not necessarily reflect the official policy or position of the Nautilus Institute. Readers should note that Nautilus seeks a diversity of views and opinions on significant topics in order to identify common ground.
Banner image is by Lauren Hostetter of Heyhoss Design
II. NAPSNET SPECIAL REPORT BY JEFFREY LARSEN
NUCLEAR COMMAND, CONTROL, AND COMMUNICATIONS: US COUNTRY PROFILE
AUGUST 22, 2019
Introduction
The nuclear deterrence forces of the United States of America have been developed over the past 75 years in order to prevent any adversary from attacking the US homeland, its forces deployed abroad, its allies and partners, and its other vital national interests around the globe. In this mission, many would argue, American nuclear force and policies have been extremely successful. There has been no major great power conflict since World War Two, and the United States has retained its position as a leading superpower.
Deterrence requires both the capabilities to threaten what an adversary holds most dear, and to convincingly demonstrate to potential adversaries that one has the willingness to carry out the threat to use those capabilities. The combination of these two elements will theoretically dissuade or deter a rational actor from taking any first step toward war, by fear of the consequences. US deterrence strategy since 1945 has relied on the credible threat of nuclear weapons use. The ultimate authority for the release of American nuclear weapons rests in the hands of the president. Deterrence requires America’s political leadership to be aware of all details surrounding any situation, to make timely decisions, and to be able to communicate those decisions with the appropriate forces. The command and control (C2) of nuclear forces is a vital piece of the US deterrence mission, and communications is the necessary link to ensure C2 over those weapons under all conditions.
Nuclear command, control, and communications (NC3) thus provides the links between nuclear forces and presidential authority. It includes early warning satellites, radars, and sensors; facilities to collect and interpret early warning information; fixed and mobile networked command posts; and a communications infrastructure that includes land lines, satellite links, radars, radios, and receiving terminals in ground stations and aboard strike vehicles.
US NC3 systems today face multiple challenges after more than two decades of neglect of its nuclear forces and NC3 infrastructure. Today, however, the United States is beginning a major modernization effort of all three legs of the nuclear triad, as well as the underlying and critical NC3 systems. Indeed, some analysts call NC3 the “fifth pillar” of the US nuclear deterrent, after the three legs of the Triad and nuclear weapons themselves.
This paper reviews the legacy NC3 system of the United States as it developed since the early Cold War. That system is in the midst of a sea-change. In late 2018 the secretary of defense appointed the commander of US Strategic Command (STRATCOM) as the enterprise lead for NC3 and its next generation architecture. The need to ensure robust existing capabilities for the current system, plus the desire to create a new system that is more than a simple modernization of existing capabilities, in a world facing more diverse threats, all while harnessing the value-added of new technologies, means that the NC3 system twenty years hence may bear little resemblance to its current arrangement.
Historical Background[1]
The first portion of the US NC3 system to be put in place was the series of Distant Early Warning radars begun in 1955 by the United States and Canada to warn of incoming Soviet bomber attack. Development accelerated after the Soviet Sputnik launch in 1957, but a rudimentary C2 system was not in place until the late 1950s, more than a decade after the development of the first atomic bomb. Prior to that point, the plan was to use commercial telephone networks and long-range radios to notify bases hosting nuclear armed bombers of their orders. President Eisenhower created a Minimum Essential Emergency Communications Network (MEECN) in the 1958 National Defense Reorganization Act. The necessity for such a communications system was obvious as the number of US nuclear weapons grew from a handful at the beginning of the 1950s to some 25,000 operational warheads by 1959, with more joining the inventory every year. Despite presidential direction, the Air Force and the Navy developed incompatible systems and infrastructure that could communicate solely with their own forces.[2]
The system developed into its modern appearance through the 1960s, with the addition of a National Military Command System, a World-Wide Military C2 System (WWMCCS), and a more responsive architecture capable of ensuring command and control over a growing triad of forces: intercontinental ballistic missiles, submarine launched ballistic missiles, and strategic bombers. Tying all this together between the three nuclear services of the era was the Joint Strategic Target Planning Staff (JSTPS) and its primary product, the Single Integrated Operational Plan (SIOP). This plan, first introduced in 1961, continued to inform nuclear planners with regularly updated versions for the next 30 years.
Many of the systems and concepts introduced in the 1960s are still used today. For example, the first Defense Support Program satellite for ballistic missile launch warning was launched in 1970; that system remains a primary element of American early warning efforts. Yet even in 1970 there were noticeable deficiencies. Undersecretary of Defense William Perry argued at the time that NC3 was “perhaps the weakest link in our strategic forces today.”[3] The last major upgrades to NC3 took place in the Reagan buildup of the early 1980s. Improvements included renovated and modernized underground command posts at SAC headquarters and the alternate NMCC site, the initial deployment of the Global Positioning Service satellite constellation, and better hardening against electromagnetic pulse effects in sensors and receivers.[4]
Following the end of the Cold War, NC3 systems faced the same 20+ years of neglect as did nuclear forces and deterrence thinking in general. Following a series of embarrassing mistakes by the Air Force involving nuclear weapons in 2007-08, investigative reports recommended a national commitment to keeping deterrence and nuclear understanding alive, including the need for a renewed look at NC3.[5] The Air Force created Global Strike Command as a way of restoring an organization with a singular focus on these matters, similar to the central role played by Strategic Air Command during the Cold War.[6]
Given the time frame since the last major upgrades, the need for a major reconsideration of how best to organize US NC3 is obvious. Many of its systems are outdated and require modernization or replacement. Senior leadership in the US government and the Pentagon have recognized this deficiency for more than a decade. It was not until 2014, however, that a Council on Oversight of the National Leadership Command, Control, and Communications System was established by Congress. This committee effort was a step in the right direction but was not enough to satisfy the Secretary, leading to the 2018 decision to designate the STRATCOM commander as the go-to individual responsible for NC3 operations and modernization.
Definitions
According to the Congressional Research Service, the Nuclear Command and Control System “collects information on threats to the United Sates, communicates that information through the chain of command to the President, advises the President on options for a response, communicates the President’s chosen response to the forces in the field, and controls the targeting and application of those forces.”[7]
To accomplish all these missions, nuclear command and control reflects a complex concept with numerous critical functions:[8]
- Situation monitoring—including the ability to collect intelligence, assess a threat, provide tactical warning and attack assessment to decision makers, and give them updates on the readiness levels of US forces. This includes gathering and sharing information on friendly forces, adversary forces, and potential targets, as well as global events of interest. The hardware requirements to do all of this are broad and demanding.
- Planning—developing war plans, including the use of nuclear weapons, so as to minimize decision time in a crisis or conflict. This may also entail adaptively planning responses during a crisis.
- Decision-making—senior military and political leaders assessing the situation, consulting through communications conferences, and considering the use of nuclear weapons in certain scenarios.
- Force management—assigning, maintaining, training, and supporting nuclear weapons, nuclear delivery vehicles, and support forces; maintaining force readiness; and ordering the dispersal or deployment of nuclear forces.
- Force direction—NC3 enables NC2 by ensuring the accurate transmission of messages executing lawful strike orders with US strategic nuclear forces or terminating operations at the end of a conflict.
Fundamentally this all boils down to three things: understanding the situation, deciding what to do, and then doing it.
NC3 has three major capability requirements that enable it to accomplish its mission of support to national command and control. First, it must provide assurance and security. This means the capability to operate with certainty to ensure information availability, integrity, authentication, confidentiality, and repudiation.
Second, the system must be reliable. It must have the capability to perform its intended functions at required levels for a specified interval, under stated conditions. Finally, it must show resilience. This is the ability to withstand, operate through, or recover quickly from difficult and unpredictable or adverse situations, conditions, or environments—the most stressful of all being thermonuclear conflict.
In 2016 the Air Force decided to identify its NC3 system as a weapons system, labeled AN/USQ-225. According to Joint Publication 3-0, a weapon system is “a combination of one or more weapons with all related equipment, materials, services, personnel, and means of delivery and deployment required for self-sufficiency.”[9] The Air Force recognized that such a designation was not a perfect fit for a large, complex system of systems like NC3, but it was the best they could come up with to highlight NC3’s importance and address the multitude of issues and myriad lines of effort necessary to ensure it meets the rigid specifications enumerated above. Depending on who you ask and how they count, the US NC3 system consists of as many as 160 different systems: satellites, aircraft, command posts, communication networks, land stations, radio receivers, and so on—a system of systems perhaps too complex for any one person to totally understand. The Air Force NC3 Center alone is responsible for 62 distinct subsystems (many of which are shown in figure 1.) STRATCOM wants a simpler and more flexible system for future leaders to come out of the ongoing modernization effort.
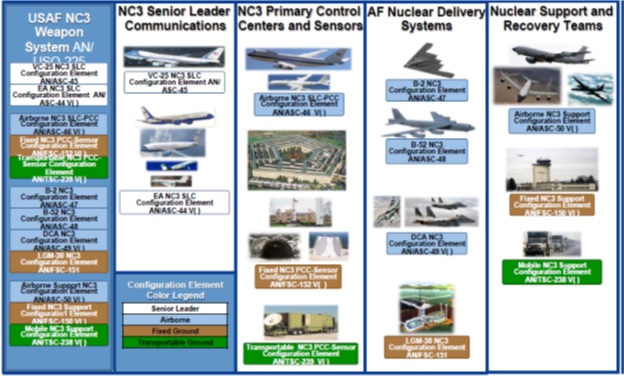
Figure 1: Representative types of systems in USAF NC3[10]
Technological Elements of NC3
Given its size, complexity, redundancy, and criticality to the nation’s survival, it is no surprise that the NC3 system has multiple parts. It may be easiest to envision it as the systems and connections shown in the simplified cloud graphic shown in figure 2.
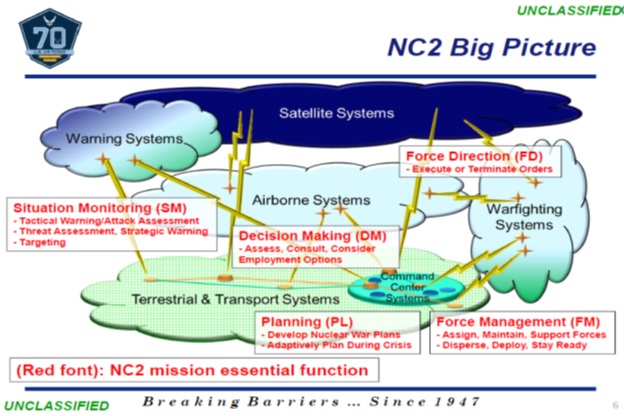
Figure 2: The Nuclear Command and Control System[11]
Warning systems include space-based satellites and ground radars that provide early warning of an adversary missile launch or potential attack. These include the legacy Defense Support Program satellite constellation, the newer Space-Based Infrared Systems (SBIRS), US Nuclear Detonation Encryptions System and sensors, and the future Third Generation Infrared Sensors. They also include terrestrial systems such as the Ballistic Missile Early Warning System, located in Alaska, Greenland, and Great Britain; over-the-horizon backscatter radars on the three coasts of the mainland USA; Pave Paws radars on the east and west coasts; Cobra Dane in Alaska; the PARCS radar in North Dakota; and the radar elements of the European Phased Adaptive Approach missile defense system being deployed in NATO. Together, these provide an overlapping set of networks that can quickly identify and attribute any missile launch directed at North America.
Terrestrial and transport systems are land-based receiving stations for the data provided by satellite networks, the physical and electromagnetic means of delivering that data to the appropriate centers for analysis, and the command posts that provide political decision-makers with recommendations and advice. If necessary, they also provide a secure conduit for orders to US strike forces.
All of these are facilitated by communications transmitters and receivers across the entire electromagnetic spectrum, from extremely low-frequency to ultra-high-frequency. Each frequency band has characteristics that make it more or less suitable in different environments. Some bandwidths are easier to jam or spoof, some work (or don’t) in an EMP or scintillation environment, some offer greater fidelity or quantity of real-time data, and so on. As a result, the US Air Force and US Navy have over the decades developed multiple means of receiving data and sending transmissions to their forces so that they can reach the bomber crews, missile crews, and submarines in any scenario. This requires a multitude of satellite constellations, each designed and deployed to take advantage of a particular capability; it also requires several different terrestrial antennas of varying sizes, including massive extremely low frequency arrays for communicating with submerged submarines. Each frequency requires the proper communications equipment for each transmission and reception. Size and weight limits often constrain how many types of systems a particular strike vehicle can carry. And in the case of submarines, the underwater environment limits which of these will be most effective in reaching the crew.
Warfighting systems comprise the three legs of the triad: bombers, intercontinental ballistic missiles, and submarine launched ballistic missiles. The specifics about the triad and the purpose for creating it in the first place are well known. Suffice to say that having three distinct systems, each of which provides the US with a guaranteed second-strike capability against any adversary, buttresses deterrence and precludes a rational actor from attacking the United States in the first place. It also reduces the risk of technological surprise that might otherwise threaten any one of the legs. For the United States, the current triad consists of approximately 66 manned strategic bombers (B-2s and B-52s) with gravity bombs and air-launched cruise missiles; 400 Minuteman III single warhead intercontinental ballistic missiles (ICBM); and 14 Ohio-class fleet ballistic submarines, each carrying some 20 MIRVed submarine-launched ballistic missiles.[12] The US Department of Energy ensures that the services providing these delivery platforms are provided with nuclear warheads for delivery on the orders of the president. These weapons systems form the backbone of US deterrence—but they won’t work without a secure NC3 system in place to get the orders to them. All three legs are scheduled to be replaced with modernized systems in the next 15 to 20 years, requiring new communication links and possibly new NC3 systems to support them and their missions.
Organizational Structure
The National Military Command System (NMCS, sometimes also called the National Command and Control System) connects all the functions of NC2 using a multitude of systems that capture intelligence, provide early warning, transmit information to the decision makers, control strike forces, and relay decisions back to those forces as necessary. Figure 3 represents a simplified version of the current NMCS system.
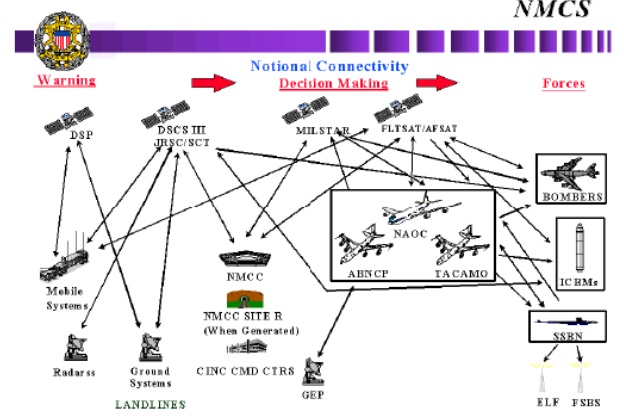
Figure 3: National Military Command System, with notional connectivity pathways[13]
The NMCS includes several core platforms and nodes, as described above. Ground stations to gather the information from space-based assets are located across the globe, including the National Military Command Center in Washington, DC, the Global Operations Center at Offutt AFB, NE, Headquarters North American Aerospace Defense Command and Cheyenne Mountain in Colorado, and large early warning radars located across North America and Europe. It also includes airborne platforms, which are primarily dedicated to command and control of the forces, such as the Air Force E-4 National Airborne Operations Center and the Navy’s E-6 Mercury TACAMO fleet.[14] There are also several types of land-based mobile backup centers.
The current responsibility for NC3 missions, equipment, personnel, training, acquisition, and maintenance is dispersed across numerous Department of Defense (DOD), Navy, and Air Force agencies and commands. The complexity and challenge of handling this was one reason for the recurring demand in official reports over the past decade that the Defense Department needed to reform the governance of the NC3 system. This process began several years ago, after similar recognition by the Air Force—which has been the lead authority for some 70 percent of all NC3 systems—that the system was basically a mess of parallel, overlapping, and complex parts that had little oversight or common vision. Over the years, the Air Force had simply added new capabilities whenever a requirement was identified, resulting in a large set of early warning and communications networks that often worked independently of one another. The rationale for every system was legitimate and fulfilled an identified operational need, but the resulting spaghetti bowl of systems was not one any rational analyst would have created.
The US Navy is considerably more tight-lipped about all things nuclear. It has designated the Chief of Naval Operations (CNO) as the responsible authority for the Navy nuclear deterrence mission, with the Director of Strategic Systems Programs responsible for providing direction and guidance on the safety and security of Navy nuclear weapons and systems, as well as the broader deterrence mission. NC3 operations fall under the Deputy Chief of Naval Operations for Information Warfare and the associated Navy NC3 Executive Steering Committee.[15]
In an effort to rationalize its organization regarding NC3, the Air Force has been tasked with modernizing the program for nearly a decade. The 2010 Nuclear Posture Review called for modernizing legacy NC3 capabilities.[16] In 2012 the Senate Armed Services Committee questioned DOD’s piecemeal approach to NC3. This was backed by a 2013 RAND study that pointed out the lack of coherent oversight of NC3.[17] As a result, in 2014 the National Defense Authorization Act (NDAA) required DOD to establish a national oversight council for NC3. This council would sit at a much higher level than the Air Force. Criticism and recommendations continued: in 2013 and 2014 reports by the Government Accountability Office pointed out problems within the NC3 community.[18] In Congressional testimony in 2014 the STRATCOM commander highlighted the need to upgrade and modernize NC3 systems. That same year a USAF Scientific Advisory Board study highlighted NC3 requirements and made recommendations for improvement.[19]
As a result of this flurry of studies and recommendations, in 2014 the Air Force Chief of Staff issued new instructions for the NC3 enterprise.[20] This top-down direction resulted in a number of organizational changes in the following three years. First, NC3 was designated as a weapons system, with Global Strike Command, headquartered at Barksdale AFB, LA, assigned as the mission area lead command. AF Material Command established an NC3 Integration Directorate in the AF Nuclear Weapons Center, Kirtland AFB, NM, and supported by the NC3 Analysis Directorate, also located at Kirtland. Training and education of new members of the NC3 team are handled by the NC3 Center at Barksdale AFB, established in 2016.[21] All of this NC3 activity, spread across the nation and involving all eight Air Force commands, was to be coordinated by the NC3 Integration Directorate, located at Hanscom Field, MA.[22]
In 2016 and 2017 new NDAAs provided additional direction to the Air Force on nuclear weapons and NC3. The Air Force was more invested in modernizing its NC3 systems than it had been in decades, but it still faced outside scrutiny. In 2017, for example, a GAO report claimed that most USAF efforts were focused on current systems vice future needs; patching existing systems rather than thinking about future requirements and new ways of doing business.[23] In 2018 the NDAA required STRATCOM and DOD to focus on NC3 related issues, resulting in direction by Secretary of Defense Mattis to General Hyten at STRATCOM to tackle this problem effective October 2018 as the sole responsible officer for US NC3 systems.[24]
The future relationship between STRATCOM and the Air Force in these matters is still being determined, but one must assume it will be much like the existing ties in the realm of other weapons systems, for example nuclear delivery platforms such as ICBMs or strategic bombers. The Air Force is the Service provider, ensuring that the combatant commander has the necessary material and trained personnel to do the job. It is the Air Force’s responsibility and mission to train, organize, and equip aerospace forces for sustained combat operations. NC3 would likely become one more weapon that the Air Force will continue to provide—and one that it is already managing. The US Navy has a parallel mission to provide fleet ballistic missile submarines (SSBNs) and submarine-launched ballistic missiles in the event of war.
Challenges to the US NC3 System
As highlighted in various US policy documents, the new world order is much changed since the Cold War and the 24-year interregnum that followed the end of that long conflict. Today the United States faces a world of great power competition and potential conflict, one that is more complex than the Cold War, with multiple nuclear powers and much-increased possibilities for war between nuclear-armed states. The NC3 system reflects the effects of neglect since the end of the Cold War, including the significant loss of expertise in all matters nuclear within the personnel system of the armed services. Furthermore, there is an inefficient diffusion of authority and responsibility for NC3 governance within the DOD. Fortunately, a consensus has developed since the Obama administration’s call for nuclear modernization as part of the Prague agenda in 2009. As discussed above, DOD, STRATCOM, and the Air Force are now working diligently to overcome years of neglect.
Operationally, NC3 faces a number of significant challenges, all of them difficult, and most of them inherent to nuclear weapons more broadly. First, the NC3 system must meet the “always-never” criteria. Just as nuclear weapons must always work when tasked to, and never go off accidentally or without proper authorization, so too must the NC3 system comply with this fundamental law of nuclear operations. NC3 must always be able to execute a legitimate order to employ nuclear force, under all circumstances. This is known as positive control. At the same time, NC3 must under all circumstances never allow the nuclear force to be used accidentally or by an illegitimate authority. This is known as negative control. Both are critical to deterrence.
NC3 must also be capable of operating in a second-strike mode—in other words, after the nation has absorbed a first strike, possibly without prior warning, and potentially one including nuclear weapons. This is clearly the most demanding scenario, with all the attendant characteristics of a nuclear environment in play. The system must also be able to deal with the blurred lines between conventional and nuclear NC3 systems. For example, it must be able to distinguish between an adversary attack on different parts of the system during a conventional conflict and recognize whether that was part of the conventional campaign or the beginning of escalation to nuclear use. This problem is magnified when NC3 systems are dual-use. This raises questions of potential miscalculation and accidental escalation due to problems of entanglement.
NC3 must also be able to survive “left of launch” efforts to degrade its capabilities. These pre-conflict operations may include cyber attack, electromagnetic pulses generated by a high-altitude nuclear burst, or even direct kinetic attack on ground-based or space-based elements of the network by hypersonic weapons, precision-guided conventional weapons, or anti-satellite weapons. The system must also be resilient enough to withstand possible insider threats, such as espionage or sabotage by disaffected individuals.
The current NC3 system is also reliant on the US civil infrastructure that provides electricity, water, and other logistical requirements to terrestrial bases that host NC3 receiving stations and command posts. This makes that element of NC3 subject to any break in service on the civilian side. The system is not completely autonomous.[25]
The current age of the American NC3 system requires nearly across-the-board modernization. The world has transitioned from analog to digital, yet the US NC3 system remains primarily analog, as it was designed prior to the age of personal computers, networked systems, or the Internet. Ironically, this means that the legacy system is actually less prone to cyber attack, and thus more secure than many more modern systems. Nevertheless, it is outdated. Decision-makers today demand ever-increasing amounts of information, including real-time photographic or video downloads from NC3 systems, thus requiring ever-increasing bandwidth capabilities. There will be a need to mate the NC3 systems necessary in the cockpits and command capsules of the future, as the United States fields new delivery platforms across the triad over the next 15 to 20 years. And there is a pressing need to replace lost expertise among the work force that designs, builds, deploys, maintains, and operates NC3 systems.
Recognizing the Need for Modernization
Although the world has become a more complex and diverse place than it was during the Cold War, the US NC3 system has not changed much to adapt to these new realities. Given the increasing number of potential threats, the challenge to American space-based assets, the rise in cyber security challenges, increased vulnerability to network attack in newer NC3 systems, and the requirement to meet the NC3 needs of an entirely new triad of nuclear forces, it is quite possible that the NC3 system of the 2030s will be very different from today. This adds yet another layer of demands on planners as they think about what might work best in the future, vice simply improving the system in place—which was originally designed, after all, for a more straightforward 1960s missile and bomber threat from a country that no longer exists.
The 2017 National Security Strategy of the United States highlighted the need to “maintain the credible deterrence and assurance capabilities provided by its nuclear triad and US theater nuclear capabilities deployed abroad.”[26] This means that significant investment would be needed to maintain the nuclear arsenal and its supporting infrastructure and to modernize the nuclear enterprise. This also means that “modernization and sustainment require investing in the aging command and control system.”
Many of the requirements for a next-generation NC3 system were enumerated in the 2018 Nuclear Posture Review. [27] It listed the initiatives required to modernize the NC3 system, including:
- Strengthening protection against space-based threats by increasing the agility and resilience of US NC3-related space-based assets.
- Strengthening protection against cyber threats.
- Enhancing integrated tactical warning and attack assessment by upgrading sensors and satellites that provide this information.
- Improving command posts and communications links by upgrading mobile command posts, ground command centers, and transmitters and terminals.
- Advancing design support technologies to enable better and faster decision-making.
- Integrating planning and operations at the regional combatant commander level.
- Reforming governance of the NC3 system.
The Secretary of Defense and Chairman of the Joint Chiefs of Staff took on the last item right away by designating the STRATCOM Commander as the NC3 enterprise lead and giving the Undersecretary of Defense for Acquisition increased responsibilities for NC3 systems engineering and integration. STRATCOM’s NC3 Governance Improvement Implementation Plan was approved in October 2018. This plan will focus on NC3 and its modernization as an “enterprise of enterprises,” encompassing the military services and other stakeholders in NC3 in an organized, holistic approach to determining and fielding the NC3 system of the future. As is already the case in the US Air Force, this approach will consider NC3 as a weapons system on par with the other parts of the nuclear triad. The two primary imperatives of the enterprise are to continue operating the current NC3 enterprise within established performance parameters, including the five critical mission functions and adhering to the “always-never” requirement and, secondly, to prepare and deliver a more rational and better designed next generation NC3 system. Of course, one danger in pursuing such a large modernization effort is the requirement to continue using and updating the “as-is” architecture while simultaneously building the “to-be” system. And there is a second danger: that modernization may mean increased complexity, which in turn may actually reduce America’s security.[28]
Conclusion
Sustainment of America’s existing critical capabilities, and acquisition of modernized systems, are core requirements to maintaining the nation’s strategic deterrence mission. The credibility of the US nuclear deterrent relies on its ability to be “believably resilient” to any attempt to disrupt US NC3 by an adversary. There is a national consensus today that the US NC3 enterprise needs to be modernized, and DOD has made STRATCOM the authority for the enterprise and its future. The US Air Force, as the preponderant force provider for the national military command and control system and its NC3 system, will be the military service most responsible for those modernization efforts. The US Navy will have equivalent responsibilities for its smaller but equally critical NC3 system connecting decision-makers with its nuclear ballistic missile submarine fleet.
Some big questions are looming over this effort, however. Does the United States simply need an updated version of what has been in place for the past 60 years? Or are there newer and better ways to accomplish the NC3 mission? These larger questions remain unanswered, at least in the public eye. One hopes that the DOD, US Strategic Command, and the Air Force and Navy are addressing them. The system is too big to continue patching and hope for the best and too critical to the nation’s survival to get wrong.
Recommended Reading
Acton, James M. “Escalation through Entanglement: How the Vulnerability of Command and Control Systems Raises the Risks of an Inadvertent Nuclear War,” International Security, Summer 2018, pp. 56-99.
Blair, Bruce. Strategic Command and Control: Redefining the Nuclear Threat (Washington: Brookings Institution, 1985).
Critchlow, Robert D., “Nuclear Command and Control: Current Programs and Issues,” Congressional Research Service, CRS Report for Congress RL33408, 3 May 2006.
Deptula, David and William LaPlante, with Robert Haddock, Modernizing US Nuclear Command, Control, and Communications, Mitchell Institute Report, MITRE Corporation, February 2019.
“DOD Nuclear Weapons Surety Program,” DOD Directive 3150.02, 24 April 2013.
Goodwin, Kristin. “Nuclear Command, Control, and Communications (NC3): Strengthening a Neglected, but Critical, Component of the US Deterrent,” in ed. S. Weiner, Nuclear Notes, 3:1, September 4, 2013, pp. 9-21, at: https://csis-prod.s3.amazonaws.com/s3fs-public/legacy_files/files/publication/120529_Spies_NuclearNotes2_Web.pdf
Larsen, Jeffrey A. and Kerry M. Kartchner, eds. On Limited Nuclear War in the 21st Century (Palo Alto, CA: Stanford University Press, 2014).
National Security Strategy of the United States of America (Washington: The White House, December 2017).
Nuclear Matters Handbook (Washington: Office of the Secretary of Defense, 2016).
Nuclear Posture Review (Washington: Office of the Secretary of Defense, February 2018).
“Nuclear, Space, Missile Command and Control: Air Force Nuclear Command, Control, and Communications (NC3),” Air Force Instruction 13-550, 2 Oct 2014.
Sagan, Scott. The Limits of Safety: Organizations, Accidents, and Nuclear Weapons (Princeton, NJ: Princeton University Press, 1993).
Schlosser, Eric. Command and Control: Nuclear Weapons, the Damascus Incident, and the Illusion of Safety (New York: Penguin Press, 2013).
“Sharpening the American Military’s Competitive Edge,” Summary of the 2018 National Defense Strategy of the United States of America (Washington: The Pentagon, 2018).
Snyder, Don, Sarah A. Nowak, Mayhar A. Amouzegar, Julie Kim, and Richard Mesic, “Sustaining the US Air Force Nuclear Mission” (Santa Monica, CA: RAND Report, 2013).
Woolf, Amy. “Defense Primer: Command and Control of Nuclear Forces,” In Focus, Congressional Research Service, 11 December 2018.
III. ENDNOTES
[1] A short overview of the history of the US NC3 system can be found in David Deptula and William LaPlante, “Modernizing US Nuclear Command, Control, and Communications,” Mitchell Institute Report, MITRE Corporation, February 2019. A more comprehensive and critical history can be found in numerous books, including Bruce Blair, Strategic Command and Control: Redefining the Nuclear Threat (Washington: Brookings Institution, 1985), Scott Sagan, The Limits of Safety: Organizations, Accidents, and Nuclear Weapons (Princeton, NJ: Princeton University Press, 1993), and Eric Schlosser, Command and Control: Nuclear Weapons, the Damascus Incident, and the Illusion of Safety (New York: Penguin Press, 2013).
[2] Kristin Goodwin, “Nuclear Command, Control, and Communication (NC3): Strengthening a Neglected, but Critical, Component of the US Deterrent,” Nuclear Notes, 2013, p. 11.
[3] Quoted in Deptula & LaPlante, p. 18.
[4] Deptula and LaPlante, p. 19.
[5] See “Report of the Secretary of Defense Task Force on DOD Nuclear Weapons Management, Phase I: The Air Force’s Nuclear Mission,” September 2008, at https://dod.defense.gov/Portals/1/Documents/pubs/Phase_I_Report_Sept_10.pdf
[6] SAC was dissolved in 1992, replaced by the new, joint, US Strategic Command.
[7] Amy Woolf, “Defense Primer: Command and Control of Nuclear Forces,” In Focus, Congressional Research Service, 11 December 2018, p. 1.
[8] Nuclear Matters Handbook (Washington: Office of the Secretary of Defense, 2016), available at www.acq.osd.mil/ncbdp/nm/NMHB.
[9] “Joint Operations,” Joint Publication 3-0, 17 January 2017.
[10] Source: “Nuclear Command, Control, and Communications (NC3) and the AF NC3 Weapons System,” PPT briefing for Nautilus conference, Stanford University, Palo Alto, CA, 23 January 2019.
[11] Source: US Air Force briefing, 2018.
[12] MIRV stands for multiple independently targetable reentry vehicles. The missiles on a Trident submarine can carry up to 8 warheads on each missile, though it is believed that their payloads are normally smaller than that.
[13] Source: CRS Report for Congress: “Nuclear Command and Control: Current Programs and Issues,” 3 May 2006.
[14] TACAMO stands for Take Charge and Move Out, a nickname for that mission since the early 1960s.
[15] “Navy Nuclear Deterrence Mission Responsibilities and Authorities,” OPNAV Instruction 8120.1A, 10 January 2018, at https://fas.org/irp/doddir/navy/opnavinst/8120_1a.pdf.
[16] Nuclear Posture Review (Washington: The White House, 2010).
[17] Don Snyder, Sarah Nowak, Mayhar Amouzegar, Julie Kim, and Richard Mesic, “Sustaining the US Air Force Nuclear Mission,” RAND Report (Santa Monica, CA: 2013), at https://www.rand.org/pubs/technical_reports/TR1240.html.
[18] “Nuclear Command, Control, and Communications: DOD Actions Needed to Better Assess Overall System Performance and Address Operational Gaps”, GAO Report 14-88C (Washington: 28 Feb 2014); and “Nuclear Command, Control and Communications: Review of DOD’s Current Modernization Efforts,” GAO Report 14-414R (Washington: 18 Mar 18 2014).
[19] “Nuclear Command, Control, and Communications,” US Air Force Scientific Advisory Board study, 2014; abstract at https://www.scientificadvisoryboard.af.mil/Portals/73/documents/AFD-140728-028.pdf.
[20] “Air Force Nuclear Command, Control, and Communications,” Air Force Instruction 13-550, 2 October 2014, at https://static.e-publishing.af.mil/production/1/af_a10/publication/afi13-550/afi13-550.pdf
[21] Barksdale also hosts Global Strike Command and the 8th Air Force with its B52 bombers. Global Strike Command would provide bombers and ICBMs to STRATCOM in the event of conflict.
[22] Author interviews at Barksdale AFB, LA and Hanscom Field, MA, May-June 2018.
[23] “Defense Nuclear Enterprise: DOD Continues to Address Challenges but Needs to Better Define Roles and Responsibilities and Approaches to Collaboration,” GAO Report to Congressional Committees, GAO-19-29, November 2018, at https://www.gao.gov/assets/700/695197.pdf.
[24] Sandra Erwin, “U.S. STRATCOM to take over responsibility for nuclear command, control and communications,” Space News, 23 July 2018; also Justin Doubleday, “STRATCOM establishes NC3 Enterprise Center,” Inside Defense, 14 February 2019, at https://insidedefense.com/daily-news/stratcom-establishes-nc3-enterprise-center.
[25] Thanks to the MITRE Report authors for this insight.
[26] National Security Strategy of the United States of America (Washington: The White House, December 2017), at https://www.whitehouse.gov/wp-content/uploads/2017/12/NSS-Final-12-18-2017-0905.pdf.
[27] Nuclear Posture Review (Washington: Department of Defense, February 2018), pp. 36-38, at https://media.defense.gov/2018/Feb/02/2001872886/-1/-1/1/2018-NUCLEAR-POSTURE-REVIEW-FINAL-REPORT.PDF.
[28] Deptula and LaPlante.
IV. NAUTILUS INVITES YOUR RESPONSE
The Nautilus Asia Peace and Security Network invites your responses to this report. Please send responses to: nautilus@nautilus.org. Responses will be considered for redistribution to the network only if they include the author’s name, affiliation, and explicit consent.



One thought on “NUCLEAR COMMAND, CONTROL, AND COMMUNICATIONS: US COUNTRY PROFILE”